-
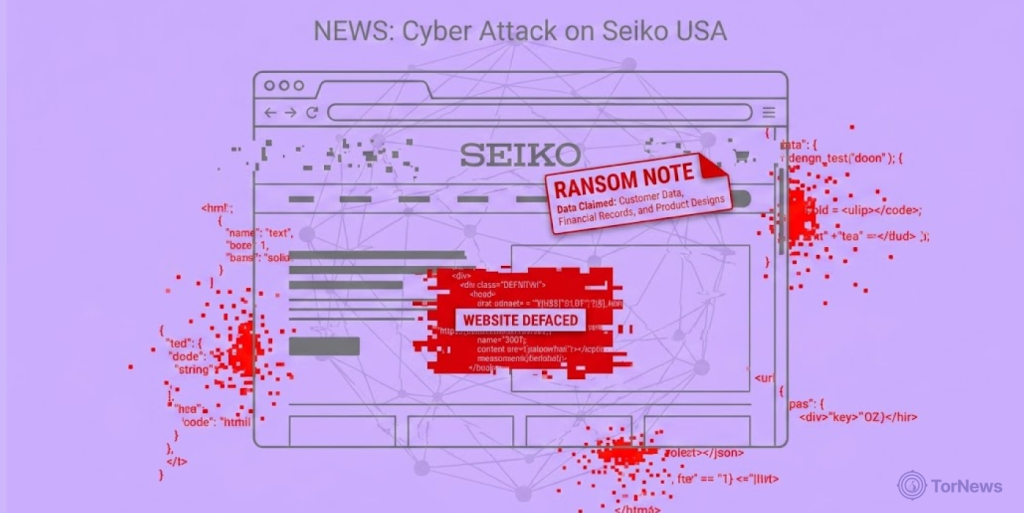
Hackers defaced one part of Seiko USA’s website, showing a “HACKED” message plus a ransom ultimatum.
-
The attackers claim they harvested the full customer database that carried emails, names, payment details, and order histories.
-
Seiko USA uttered no official response, leaving the investigation in the hands of cybersecurity experts.
The Japanese watchmaker’s US unit is currently facing a huge cybersecurity issue. Unknown web thieves hacked into Seiko USA’s site and left them with an ultimatum: either complete negotiations or the company will suffer a full public data dump.
The attack surfaced in the “Press Lounge” section of the company’s website, where the bad actors replaced the normal web content with a defacement page announcing that they had compromised the backend of Seiko’s Shopify.
According to the attackers, they stole customer names, phone numbers, shipping addresses, email addresses, payment-related information, and purchase history.
Hackers Set a 72-Hour Countdown
Apart from defacing Seiko USA’s website, the attackers created a defacement page that provided detailed instructions on how Seiko USA could find a particular Shopify customer’s account ID (8069776801871) in their admin panel.
The attackers also confirmed an email linked to that account, telling Seiko USA to reach out for negotiations through that profile.
The bad guys warned Seiko USA that if they did not contact them within 72 hours after the defacement, they would either publicly publish the hijacked data or market it on dark markets.
Seiko USA removed the defacement page from their website, but so far they have not confirmed the breach or given any public statement regarding the claims made by the attackers. Analysts are looking into the situation as investigators dig behind the scenes.
The company’s silence has drawn significant attention in the cybersecurity community, particularly due to the fact that the attackers provided what looked like specific technical identifiers to support their claims.
Shopify Backend Becomes the Entry Point
According to cybersecurity analysts, cybercrime is now taking on a new type of attack. Criminals used to only attack companies through their hard drives and servers, now the current trend has criminals attacking 3rd party applications and services instead.
Easy access points are targets and one of the most popular is through cloud-based e-commerce platforms like Shopify. This is because one compromised account or poorly configured user access permission could potentially expose customer databases.
Former IPS officer and cybercrime veteran Professor Triveni Singh made comments regarding this incident and stated that “cyber thieves create large amounts of data breach by taking advantage of social engineering techniques and weaknesses that exist within cloud based ecosystems.
In services like Shopify, a single account at risk can jeopardize an entire customer database. Organizations should adopt multi-layered security modifying methods to minimize their risk.”
Cyber experts suggest that cybercriminals have evolved defacement attacks from just being an interruption of website function. Cybercriminals now treat stolen data as an asset to sell on secure black markets or as leverage to request ransom requests from organizations.
The Mercedes-Benz USA data sale claim is a prime example of this trend, hackers allegedly offered customer information for sale on the dark web, demonstrating how stolen data has become a commodity traded alongside other illicit goods.
What the Breach Reveals About E-Commerce Security
Following the Seiko USA incident, how secure e-commerce platforms store sensitive data of customers is now a global concern. According to security analysts, many companies are at increasing risk for these types of attacks because of their extensive reliance on cloud infrastructure without consistently conducting audits and implementing adequate access controls.
Meanwhile, no official response yet from Seiko USA concerning the data breach. But cybersecurity teams are assessing the near-term impact to figure out the origin of the breach and any potential link to the bad actors.