-
Hackers attack AstraZeneca’s Internal Systems, steal sensitive information, and display it for sale on the dark web.
-
This is just one in a series of increasingly frequent cyberattacks against large pharmaceutical and healthcare firms that have valuable research data and other types of corporate information.
-
As opposed to ransoming data back to corporations, hackers are now using stolen data as a way to make money from other criminals, making it more challenging for law enforcement organizations to track and contain cyberattacks.
A significant cyberattack has hit the drug manufacturer AstraZeneca, as attackers claim they stole a substantial amount of internal data and have posted it for sale on the dark web.
While AstraZeneca produces and sells medicines for countless people globally, the problems of cybersecurity issues within the healthcare industry have once again increased.
According to some security experts, the hackers gained access to possibly multiple gigabytes of internal files, including operating system details, and possibly worked with certain items consisting of staff members’ data. AstraZeneca is currently assessing the breach’s severity and determining what specific data may have been involved.
What the Hackers Stole and Why It Matters
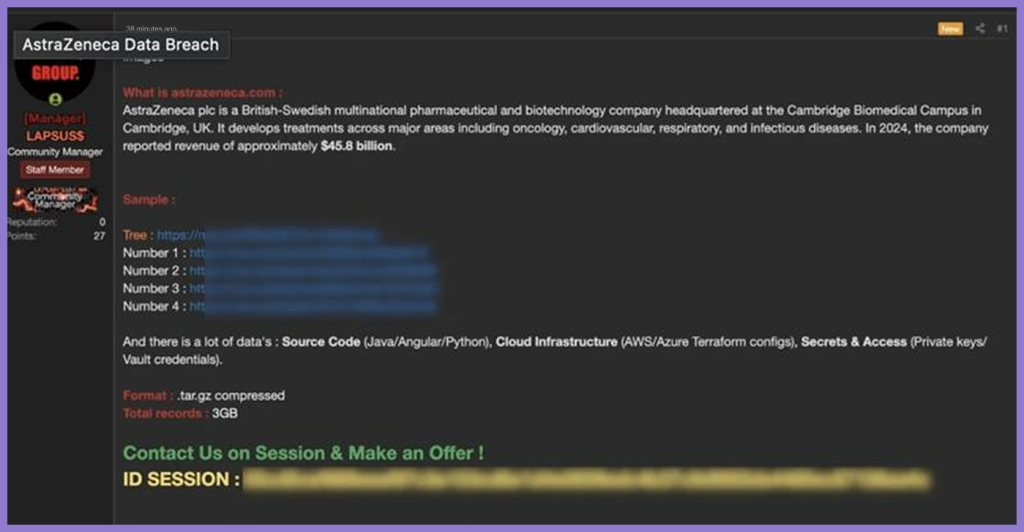
The report indicates that the hackers, LAPSUS$, stole a substantial quantity of internal technical information, but not any customer or patient-specific data. Although this may sound less disturbing, information technology security experts state that when a hacker has obtained usernames and passwords to an organization’s systems as well as other types of internal data, that information allows them to search for vulnerabilities in the organization’s network and may provide them with access to perpetrate a future attack.
Selling stolen data on the dark web has become a major method of operation for cybercriminals. As compared to requiring a ransom payment from their victims, many hackers now sell information to other criminals and make money upon completion of the sale, while making it difficult for law enforcement to track them.
If the breach is indeed valid, this could represent one of the more serious cyber incidents to impact the healthcare industry in the year. This warning describes the increasing concern from cybersecurity experts of the cascading impact that such attacks will likely have on the entire global healthcare delivery system.
Why Big Companies Are Facing Hits More Often
Large corporations are facing attacks from cybercriminals today, and this is happening on a large scale. They have an abundance of data, and they are continually the targets of such hits. Hackers target the healthcare, financial, and technology sectors for the valuable data they hold, such as trade secrets, proprietary business information, and insights into how products are developed or manufactured.
The U.S. Cybersecurity and Infrastructure Security Agency reports that cybercriminals have increased their attacks on these industries in recent years, especially in terms of data theft and ransomware attacks. Additionally, the increased reliance on digital systems and cloud services has given cybercriminals many more opportunities to intercept and infiltrate victim networks.
Over the last several years, there has been a growth in the organization of criminal groups that target these organizations’ infrastructure. They use many resources to build sophisticated methods for committing cybercrimes and share information among themselves.
As a result of collaboration between these various criminal groups, attacks occur more frequently, but their rate of success is typically much higher than in the past.
These attacks increasingly target source code, as seen in the Mideast breach, where hackers stole 40GB of data, including complete application source code, proving that cybercriminals are moving beyond just customer data to target the intellectual property that makes companies operate.
The Bigger Picture: A Growing Global Risk
AstraZeneca’s recent hack is just one example of how they are now a huge risk for large organizations globally, as it truly is a business issue. These incidents not only cause data loss but also inflict significant damage on an organization’s reputation and client trust. Companies must also now protect themselves from this loss of business, and how much they spend on security could increase because of it.
Governments and businesses are also reacting by increasing their budgets for cybersecurity, and they are doing more to protect themselves by putting in place better processes and systems. According to the European Union Agency for Cybersecurity, companies should be working together to improve their ability to share information on cybersecurity and attack types with one another.
The overall takeaway from the attack on AstraZeneca is that all of the biggest and best companies can suffer attacks. The consequences of this attack will extend well beyond just the loss of data for a supplier of critical medicines and have the potential of inflicting harm or disruption on many more organizations throughout the supply chain.