The dark web is often portrayed as a hub for hackers selling stolen data, but it’s also a valuable resource for security and privacy professionals.
With the right tools, you can check if your emails, passwords, or sensitive data have been exposed in breaches without engaging in anything illegal.
Dark web investigation tools scan hidden forums, leak sites, and ransomware databases to alert you if your data is at risk.
In this guide, we’ll cover seven powerful tools, both free and paid, and explain how to use them safely and legally to protect your information.
Best Dark Web Investigation Tools – Quick List
Here’s a quick look at seven tools that help you investigate dark web data exposures. Each serves a different purpose, from automated monitoring to deep manual searches. This dark web tools list covers both commercial platforms and free options:
- Social Links: An AI-powered OSINT platform that provides a single dashboard, allowing users to search social media, blockchains, and the dark web.
- Rapid7: A comprehensive threat intelligence tool for monitoring stolen data and threats on brand on dark web sources.
- Skopenow: An automated OSINT tool that combines AI for analyzing the dark web, social media, and surface web data, and is useful for investigations.
- Webz.io: This is a machine-readable data feed that provides structured dark web information for integration into security tools.
- DarkIQ: A continuous dark web monitoring tool profitable to security teams and MSSPs.
- BreachSense: An API-based system for tracking criminal forum logs in real-time whenever a new log is created.
- SpiderFoot: It is an open-source tool that automates all of the Open Source Intelligence scans from various data sources over 200 and has dark web findings as well.
What is Dark Web Investigation?
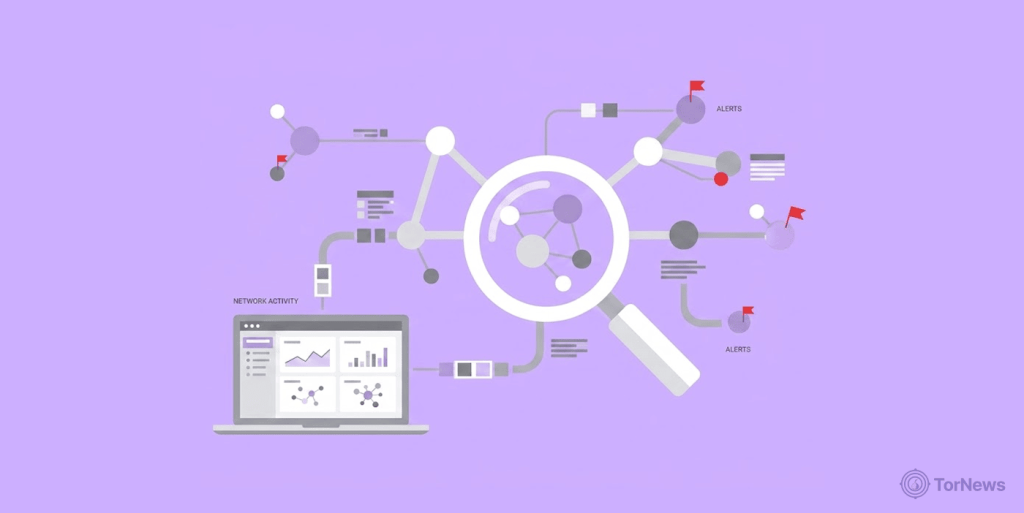
Dark web investigations refer to searching and monitoring exposed data, compromised names and password combinations, or illegally obtained company information, and tracking all the cybercriminal behavior using open source intelligence (OSINT) techniques via anonymous internet servers.
When searching for data on the dark web, cyber investigators are primarily looking for documents, emails, codes of conduct, and hacked personal information related to an organization’s company name. The areas of concern include:
What Investigators Look for
- Leaked usernames and passwords resulting from data breaches.
- Data owned by companies goes beyond the email or password.
- Possible ransom mentions on a ransomware group’s leak site.
- Threat actor discussions relative to targeting an organization or industry.
- Businesses are represented on fake online sites or social media platforms by impersonating companies’ brands.
Investigators Typically Conduct Dark Web Investigations
- A company’s risk and security officers are monitoring their own organization’s exposure.
- Law enforcement agencies are tracking the cyber activity of criminals.
- Independent reporters investigating leak stories related to whistleblowers.
- Individuals verify whether their own data has been compromised.
The purpose of conducting these investigations is to gather intelligence to allow an organization to respond more quickly when its data is located in unauthorized or inappropriate places.
In many instances, conducting an investigation on the dark web can be the difference between identifying and mitigating a data breach quickly vs. finding out months later that criminals have used stolen data against your business.
Why Dark Web Investigation Tools Matter

You may be asking yourself: “Why care about investigating the dark web?” The answer is simple: that’s where your stolen data ends after hackers obtain it.
Most people think hackers hold onto their data once they steal it, but that’s generally not true. They will sell the stolen data on dark net marketplaces, distribute it through private Telegram channels, or make it publicly available via data breach leak sites when the victim refuses to cooperate with them.
If you don’t monitor these outlets, you won’t know whether your data has been compromised until it’s too late, such as when someone tries to access your banking credentials.
According to the IBM 2025 Data Breach Cost Report, organizations typically take an average of 241 days to recognize and remediate data breaches. That is escalating to nearly eight months during which attackers have access to your systems.
But by implementing dark web monitoring tools, the time gap is drastically reduced. For instance, using BreachSense allows you to receive alerts within hours, compared to months when credentials appear in a stolen log.
For any security team, using dark web investigation tools is a critical aspect of threat intelligence. These tools can reveal attacker tactics, identify compromised assets, and even expose stolen credentials before incidents fully develop.
They also help individual users feel secure because they provide a venue to check if their email and/or password have been compromised, and they do this without the need for individuals to search through potentially dangerous websites manually.
Dark web investigation is just one piece of the privacy puzzle. For a broader approach to protecting your digital footprint across the clear web, social media, and everyday browsing, explore our roundup of the best online privacy tools.
The dark web investigation tools, free and paid options covered in this guide, give you that visibility. They turn the dark web from a mysterious threat into a manageable intelligence source.
Top Dark Web Investigation Tools – Detailed List
Let us examine every instrument individually by addressing critical areas for each. We will discuss a brief overview of the instrument, some key features, an explanation of how each of the instruments works, the target audience, and the costs associated with the instruments:
1. Social Links
Social Links is an open-source intelligence (OSINT) tool that utilizes artificial intelligence to collect and organize data from over 500 sources. Law Enforcement, military, and Fortune 500 companies utilize Social Links to perform comprehensive research across medium-sized groups of the population, social media networks, instant messenger platforms, cryptocurrency blockchains, and on the dark web.
It aggregates digital information it collected from a wide range of sources, including social media networks (i.e., Facebook & LinkedIn); Instant Messenger Platforms. The large number of sources allows researchers to follow subjects where they exist in many technological media.
The machine learning model continues to improve with experience based on previous investigations, thereby enabling users to spend less time filtering out noise from an investigation, and the person doing the investigation has more time to focus on the actual credible intelligence.
The application tracks the movement of illicitly obtained funds through the scanning of blockchain transactions. Built-in features of the site allow an individual to search for dark web marketplaces without disclosing their true identity.
Corporations, government agencies, and professional investigators who require Military-Grade intelligence without custom programming. Commercial variable pricing. No free version available.
2. Rapid7
Rapid7 Threat Command is an all-in-one threat intelligence platform that helps organizations identify security threats from the clear web, dark web, and technical sources. It provides organizations with continuous visibility into stolen data, brand abuse, and emerging threats.
It monitors hundreds of thousands of dark web sites, forums, and paste sites and identifies when someone mentions your organization, domain names, email addresses, or other assets.
The tool collects intelligence from more than 600,000 intelligence sources, including private Telegram channels, ransomware leak sites, hacking forums and invite-only criminal communities.
Once the tool identifies fraudulent content, phishing websites, fake social media accounts, brand impersonations, it automatically initiates the takedown request process. You decide what keywords, domains, or threat levels the tool will use to notify you through email, Slack or directly into your ticketing system.
The ideal choice for security teams, incident responders, and brand protectors in need of continuous monitoring and the ability to remove or delete content found. For commercial services (custom pricing). Contact Rapid7 for a quote.
3. Skopenow
Skopenow provides automated OSINT investigative capabilities via an AI platform that searches for, analyzes, and aggregates dark web, social media, and surface web data sources. Security teams, law enforcement agencies, and corporate investigators use it to rapidly evaluate threats and collect intelligence.
When you enter your target, Skopenow will automatically collect data from the dark web, e-commerce sites, and social media platforms without the need to search each site manually. It processes and returns the data to you in just minutes instead of days.
The tool uses advanced natural language processing to analyze text and images for threats, sentiments, and relationships within the various types of data it collects. Skopenow produces visual maps showing connections among persons, accounts, and events relevant to investigations performed on behalf of an organization.
It is ideal for corporate security teams, due diligence, and law enforcement looking for automatic court-admissible intelligence. Commercial (custom pricing); Call to request a demo or submit an order.
4. Webz.io
Webz.io has APIs that give you structured data from the dark web in machine-readable format. This is data for organizations that wish to add dark web intelligence to their current security tools. Webz.io provides Lunar as its dedicated dark web feed, which delivers structured data from hidden services.
It converts unstructured raw HTML dark web data into machine-readable structured data (like JSON). This will allow your tools to perform an analysis and take action on the data immediately, without having to parse the data.
It provides years of archived dark web data for retrospective investigations into the past. If you discover today that a breach occurred, you can search for your data from months earlier to better understand what the incident may have impacted.
The platform updates new dark web data as soon as it becomes available, with minimal latency. The platform covers .onion sites on the Tor network, Tor network forums, Tor network dark markets, and Tor network ransomware leak pages. You can avoid the headaches of maintaining your own Tor infrastructure or the limitations of using other Tor exit nodes.
The organizations that have an internal security department that is looking to develop their own monitoring solution through Custom Development as opposed to using existing dashboards. The service uses a commercial, usage-based delivery model and also offers a free tier with limited access.
5. DarkIQ
DarkIQ is designed to enable security teams to easily monitor the dark web for mentions of their organizations. It’s automated, continuous monitoring system provides real-time and automatic discovery of dark web credentials without requiring any technical knowledge or direct access to the dark web.
The application will continuously check for any mention of the organization in dark web sources like; dark web forums, darkweb markets, dark web references, etc. It can search through thousands of dark web sources to identify any credentials, usernames, passwords, emails, that have been compromised.
It monitors all hackers who have a blog outlining information on their victims. If the attacker has published the victim organization, the organization using DarkIQ will get a notification of the exposure in hours, typically before the attackers actually publish any data.
Security personnel and Managed Security Service Providers (MSSPs) who need complete dark web monitoring, but cannot perform lengthy manual research. Commercial (by subscription). Pricing is dependent on the volume of monitoring.
6. BreachSense
The BreachSense is a security solution that monitors the dark web for security threats to organizations and managed service providers. It works by detecting stolen credentials in real time from malware and other illegal activities that occur through various means, such as hacker forums, and other methods attackers use to distribute information about the credentials they have stolen from victims.
Infostealer viruses are one of the largest threats facing security professionals today. These viruses can be installed on infected systems, and as they operate, they will store every username and password typed into a user’s computer. Stolen credentials are often stored on the dark web as hash codes instead of traditional plaintext. This will allow you to perform force resets on weak passwords.
Attackers can utilize stolen session cookies as the first option when attempting to breach a system because they can assume complete control over accounts without multi-factor authentication.BreachSense monitors ransomware leak blogs for announcements for victims of stolen data.
It is ideal for organizations that need quick, automated alerts and integrations with their current security stack via API. Commercial (custom pricing). A free trial is available upon request.
7. SpiderFoot
SpiderFoot is an open-source automated OSINT scanning solution that gathers data from more than 200 publicly available databases and allows you to obtain relevant data about your target domains, IPs, e-mails, and/or user accounts. It comes with a web user interface and a command-line interface (CLI) version which caters to a wide variety of skill levels.
It queries data from an extensive list of OSINT sources like Shodan, VirusTotal, HaveIBeenPwned, WHOIS records, DNS databases, social media, dark web modules, etc. Each investigation allows you the option of selecting which modules to run based on your particular needs. If you need just a DNS lookup, run the DNS modules only.
Searches for mentions of your investigative objects from hidden services. The website’s UI allows beginners to utilize SpiderFoot, while the command-line interface enables the power user to have scripted access to the program.
Free, comprehensive OSINT tools that are very easy to use as well as strong enough to use by professionals. Free, open source (Self-hosted). SpiderFoot HX (Paid), Cloud-based multi-user access and API access.
Are Dark Web Investigation Tools Free?

Many people ask this question, and the answer depends on what you want to find out.
There are certainly free tools available that can work well for basic investigations. An example is SpiderFoot, an open-source tool that is free to use and can be very helpful when conducting investigations. However, it does require a fair amount of technical know-how in order to set up and run successfully.
For readers specifically looking for no-cost options to check if their personal data has been exposed, we’ve compiled a dedicated list of the best free dark web scan tools that are both safe and beginner-friendly. Security professionals across the globe widely recognize and trust this tool.
Freemium tools (i.e., where you get some level of access for free, but need to pay for continued use or additional functionality) exist as well. An example is Webz.io, which provides limited access to its API for free. This would work fine for someone who needs to perform a few occasional searches, but not really for someone who needs to have continuous monitoring.
For those seeking more sophisticated solutions, several paid tools serve as market standards, including Social Links, Rapid7 Threat Command, Skopenow, DarkIQ, and BreachSense. All of these tools provide automation/real-time alerts and dedicated support for organizations that must monitor for exposure 24/7 and cannot afford to have exposure go undetected.
So the short answer is YES, some of the best dark web investigation tools free available. SpiderFoot is, without a doubt, one of the best of these. However, “free” also means you may have to sacrifice your time and/or expertise in using these.
If you’re comfortable using command lines and have enough time and desire to manually perform these scans using free tools, then they are great solutions. However, if you need to know as soon as your data is found in a stealer log, then it will likely require a paid service.
Is Dark Web Investigation Tools Safe and Legal?

This is of utmost importance. The answer is “YES,” but there are limitations to their use.
Legality
Using these tools to investigate your own data or your company’s assets is perfectly legal. You own those assets and information; you have the right to know if they were compromised.
However, using these tools to investigate others without their consent (individuals, organizations) can be a violation of privacy laws (i.e., GDPR) and/or may also be a breach of authorization to access those assets. So, you must have a written authorization before you start probing any third-party targets.
Safety
Investigating illegal content on the dark web can expose you to bad actors and malicious content, which means your safety is at risk. That’s why safety practices are critical:
- Use an isolation approach: Conduct your investigation using a virtual machine that has no link to your personal or business networks.
- Maintain passiveness: Do not log in, post, or otherwise participate in activities on the dark net. Just observe and collect.
- Use tools that anonymize access: Platforms like Social Links and DarkIQ provide built-in anonymized access; you never touch Tor directly.
- Follow the law: Keep documentation of the required consent for each target you investigate. If unsure whether you have documentation, consult with your legal counsel.
When used responsibly, dark web investigation tools and safe and legal practices are entirely achievable. Most commercial tools are designed with compliance in mind and include features that help keep investigators safe.
Final Word
The best dark web investigation tool depends on your needs and expertise. SpiderFoot is ideal for beginners seeking a free, reliable scan, while BreachSense suits professionals with real-time alerts and deep breach monitoring.
For advanced, visual investigations, Social Links or Skopenow offer powerful analysis tools. Agencies managing multiple clients can rely on DarkIQ or Rapid7 Threat Command, while Webz.io is best for custom data integrations.
Ultimately, dark web investigation is about protecting your data. Use these tools responsibly to gain valuable security insights.