-
Massive data theft, hackers stole 4TB of data from Mercor AI, including 939GB of source code, a 211GB user database, and 3TB of video interviews and passport scans.
-
The breach occurred through a backdoor injected into the popular LiteLLM open-source tool, which the hackers then used to compromise Mercor’s VPN.
-
The notorious Lapsus$ group is auctioning the stolen data on the dark web, posing serious security and privacy risks to the company’s $10 billion recruitment platform and its users.
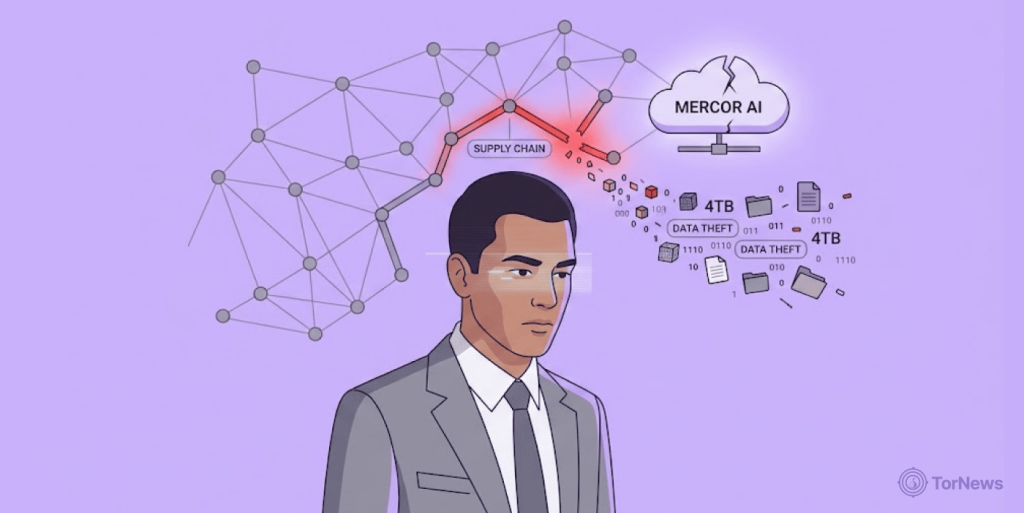
A major artificial intelligence recruitment company has become the latest victim of a damaging supply chain attack. Mercor AI, a platform with a valuation of $10 billion, confirmed that hackers stole 4 terabytes of sensitive data from its system.
The notorious hacking group Lapsus$ has taken responsibility, it is now auctioning the stolen information on the dark web.
How the Attack Happened
The breach did not come from a direct attack on Mercor’s own walls. Instead, it started with a vulnerability in a popular open-source tool called LiteLLM, which many AI companies use. In late March this year, a hacker, TeamPCP, gained access to the publishing credentials for LiteLLM. They injected a hidden backdoor into two versions of the software, 1.82.7 and 1.82.8.
Because LiteLLM is software that most companies widely integrate into AI applications, the malicious code spreads quickly. When Mercor installed the update, the backdoor allowed the hackers to slip through the company’s Tailscale VPN. From there, they claim to have taken a massive amount of private information.
According to cybersecurity experts, the stolen data includes 939GB of source code, a 211GB user database, and 3TB of storage buckets containing video interviews and passport scans used for identity verification.
Mercor’s Response and the Hackers Took
Mercor AI officially confirmed the breach, stating that it was the direct result of the LiteLLM supply chain attack. In its statement, the organization is taking measures to remedy this situation while working closely with experts in the forensics field from external agencies to assess the total impact of the situation. Also, it emphasized that protecting both customer privacy and contractor privacy will remain their primary focus.
The potential impact of the incident could pose critical risks to the company and those around it. Mercor was established in 2023, and it connects companies that are looking for professionals to work with and companies that are at the cutting edge of artificial intelligence, like OpenAI and Anthropic, and others. It processes almost $2 million in daily transactions and generates about $500 million in annual revenues.
The potential compromise of Mercor’s Private Application Programming Interfaces (APIs) through this attack could expose a weakness in the security of the company. Also, their contractors could have their Personally Identifying Information (PII) compromised or used for identity theft as a result of the exposure.
The Threat from Lapsus$
The Lapsus$ hacking group takes responsibility for the latest attack on Mercor. Using aggressive extortion methods to target large technology firms, the group has made a name by leaking information or auctioning data on the dark web in order to compel companies to pay a ransom.
By listing Mercor’s data for sale and asking interested buyers to “make an offer,” they are continuing their pattern of public humiliation and financial blackmail.
Once the group launched a data extortion attack on a company or organization, it would demand a ransom by threatening to expose the stolen sensitive data. Lapsus$ uses various methods to carry out its attacks, including social engineering via phishing, vishing, and spear phishing, to exfiltrate credentials.
Also, the group can infiltrate people’s personal email accounts or use SIM-swapping tactics to gain access to its target’s passwords and other data it needs. This incident highlights a growing danger in the tech world, attackers are increasingly targeting small, trusted software tools to gain access to much larger companies.