-
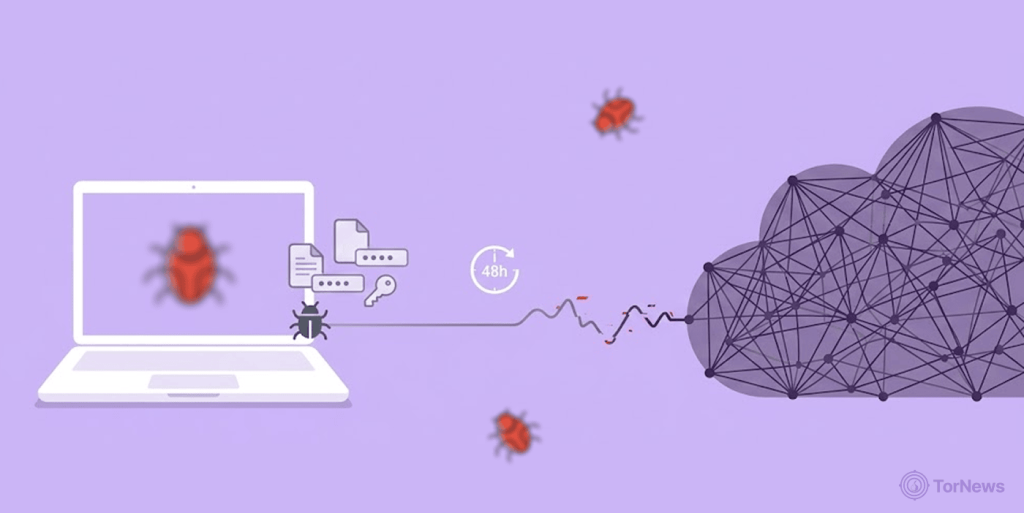
Research has revealed that infostealer infection can lead to dark web data leaks within 48 hours of infection.
-
Session cookies are the most dangerous target; they let hackers bypass multifactor authentication completely.
-
The underground economy relies on families like Lumma, RedLine, and Raccoon to turn stolen data into profit before companies even notice.
Before now, everyone thought data breach takes weeks to discover. For most companies, that’s true, but for infostealer malware, the timeline is very much shorter.
According to research, it takes only a single bad file download by one employee, and the clock starts ticking. The malware will harvest company login credentials and within 48 hours, the information is already up for sale on dark web markets.
Infostealers’ 48-Hour Lifecycle
If a worker downloads an infected software on a Wednesday afternoon. By Friday morning, their corporate login is already for sale on a dark web marketplace. The infection, the data harvest, and the sale all happen before the security team even sees a red flag.
The process begins fast. The first two hours is the entry window, when the user clicks a malicious file. The vectors are usually cracked productivity apps employees try to install to make work easier. Sometimes YouTube tutorials or even malware laden ads on legitimate sites.
These strains of malware are fast-moving and stealthy in nature. It’ll enter quietly, quickly retrieve any data it wants, and usually self-delete before any antivirus application has an opportunity to detect and flag it.
Between hours two and twelve, the real damage happens. The malware digs through browser profiles, targeting SQLite databases. It pulls out saved passwords, session cookies, and cryptocurrency wallet details.
Session cookies are the gold here. This data enables the attackers to slip past multifactor authentication with practiced ease. But that’s not where it ends. The malware also collects system metadata, VPN configurations, and cloud credentials. It bundles everything you’ve ever saved into a single package.
The Listing in Dark Web Marketplaces
The stolen data flows into a well-organized underground economy. A few dominant malware families control most of the action.
Lumma Stealer leads the pack as the most prevalent option. It offers advanced anti-detection and focuses on browser credentials, crypto wallets, and auth tokens.
RedLine Stealer runs as a malware-as-a-service operation, pulling data from over 80 applications even after recent law enforcement efforts against it.
Raccoon v2 targets crypto wallets mostly, while Vidar uses a pay-per-install model spread through malicious ads. The bad actors behind these tools constantly update them. Their goal is to stay ahead of detection and maximize the data they steal.
How to Fight Back
Traditional security often misses this entire process. By the time a forensic team starts investigating, the credentials have already changed hands.
This is where proactive monitoring comes in. Dark web monitoring solutions watch dark web markets for fresh logs. If an infostealer infects an employee’s device and their credentials appear for sale, the security team gets an alert within the critical 24-hour window.
While companies focus on protecting their data, the mental health of those who operate in these spaces is increasingly becoming a concern for researchers, who warn that the anonymity and illicit nature of dark web activity can lead to severe psychological consequences for frequent users.
That early warning gives administrators a fighting chance. They can revoke access, kill active sessions, and lock down the compromised account. The goal is to act before an initial access broker sells the entry point to a ransomware crew. The infostealer epidemic is about speed. The key to surviving it is responding before the exploitation even begins.