-
A dark web platform called Darkhub has surfaced on the Tor network, openly advertising commissioned hacking services that range from social media account takeovers to cryptocurrency fraud. Often, such platforms are scam.
-
Researchers at Oasis Security traced the platform to a publicly exposed IP address and a hosting provider with a documented record of bulletproof hosting behavior.
-
Darkhub’s “fund recovery” and credit score manipulation listings carry the signature of advance-fee scam operations, suggesting the platform may be targeting its own paying clients alongside outside victims.

A dark web platform named Darkhub has appeared on the Tor network, openly selling hacking-for-hire services to anyone with a payment to make. The platform packages a wide menu of illegal capabilities into a clean, organized interface, presenting criminal services as if they were standard digital products available to any buyer.
What sets Darkhub apart from similar dark web operations is how openly it markets these capabilities. There is no pretense. The platform positions itself as a one-stop shop for commissioned digital crime, lowering the barrier to entry for anyone without a technical background who wants to order an attack. From our experience, what we can tell you, however, is 99% of such platforms launch to scam people online.
Darkhub Advertises Social Media Takeovers, Phone Surveillance, and Bank Account Access
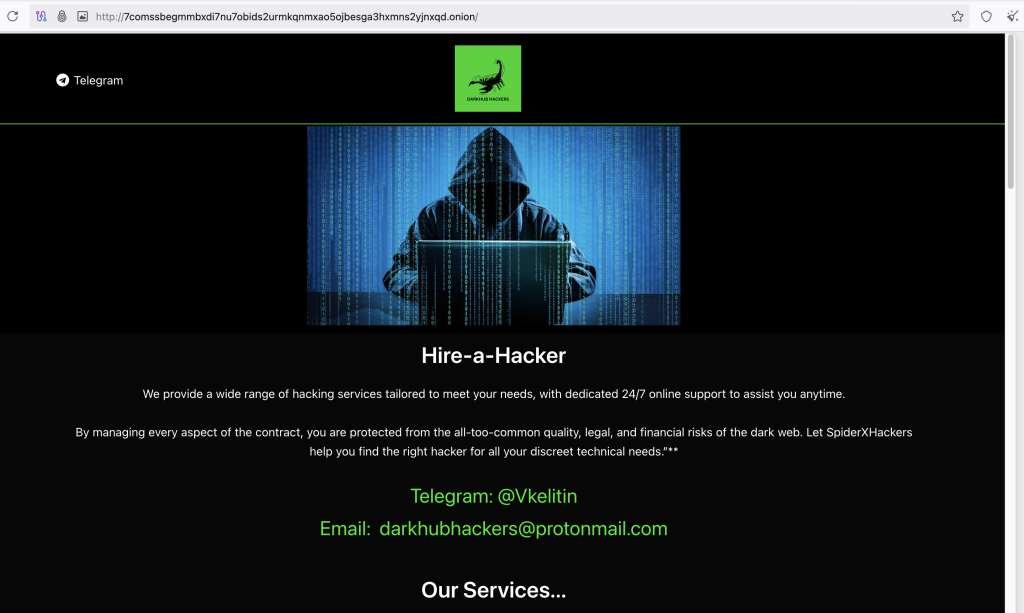
Darkhub lists services covering nearly every recognizable form of digital intrusion. The platform advertises unauthorized access to Instagram, Telegram, and WhatsApp accounts, along with email compromise, mobile phone monitoring, and real-time location tracking of individuals.
It also lists cryptocurrency fraud services, unauthorized bank account access, and credit score manipulation, assembling a broad criminal catalog in a single storefront. By offering these capabilities as a paid service, Darkhub makes it possible for anyone to commission a digital crime without any specialized knowledge.
The platform directs buyers to a Telegram handle (@DarkHubs0) and a ProtonMail address, keeping all interactions deliberately anonymous and giving the operation the appearance of a structured, running business.
Crypto Fraud Listings and Recovery Scam Signals Raise Double-Threat Concerns
The cryptocurrency-related listings on Darkhub drew particular attention from researchers at Oasis Security, who identified and analyzed the platform. Crypto fraud ranks among the fastest-growing categories in cybercrime, and Darkhub makes those capabilities available as a paid service, meaning anyone can commission digital theft involving digital assets without any technical skill of their own.
The more telling detail, however, sits right alongside those crypto listings. Darkhub also advertises “fund recovery” and credit score manipulation, two categories researchers identify as hallmarks of advance-fee scam operations. These schemes, in particular, focus on those who have already been defrauded, giving them high hopes of recovery in exchange for an upfront payment that goes forever.
Their presence in Darkhub’s catalog suggests the platform may be running a layered operation, targeting outside victims through recovery promises while simultaneously collecting fees from paying clients for hacking services it may never actually deliver.
Many dark web platforms advertising offensive capabilities operate this way in practice, taking payment without ever providing anything real. Darkhub’s actual technical capability cannot be confirmed through external observation alone, but the warning signs throughout its service listing are difficult to ignore.
Oasis Security Ties Darkhub Backend to Bulletproof Hosting Infrastructure
Oasis Security’s investigation uncovered a significant operational detail. Darkhub, despite running on the anonymity of the Tor network, has an IP linked to its backend system. This address is open to the public to route. That exposure is notable for any service that depends on staying hidden.
Using the platform for dark web intelligence, Arthur, that IP pointed the researchers back to a hosting provider in the U.S, running under ASN AS44259, as ULTAHOST. Third-party reports have previously flagged this provider for bulletproof hosting characteristics, meaning it routinely ignores abuse complaints rather than acting on them.
ULTAHOST has also faced an ICANN compliance notice linked to phishing-related domain abuse, and its own marketing reportedly emphasizes lenient content policies, making it a natural fit for cybercriminal operations that cannot risk losing their infrastructure.
The IP address associated with Darkhub has not held steady over time. Historical data shows it changed multiple times before settling at its current value as of January 12, 2026.
Whether those shifts reflect provider migrations or deliberate operational adjustments remains unclear. The key indicators tied to Darkhub include its Tor hidden service address, a partially redacted public IP (38.127..), the AS44259 hosting infrastructure, the operator email darkhubhackers[@]protonmail.com, and the Telegram contact [@]DarkHubs0. Organizations monitoring dark web threats should treat any traffic connected to this infrastructure with serious caution.
As platforms like Darkhub emerge to facilitate cybercrime, the dark web continues to be a hub for leaked corporate data. In a recent high-profile incident, a hacker group leaked data allegedly stolen from Asahi Group, serving as a reminder that no organization is immune to dark web-enabled breaches. For full details, see hacker group leaks data allegedly stolen from the Asahi group on the dark web.