-
Hacker group UAT-8302 with ties to China has been going after government agencies in southeastern Europe and South America.
-
The group uses malware tools shared with other China-aligned hacker groups, making it hard to track.
-
Researchers say this indicates close working relationships between multiple Chinese hacking operations.
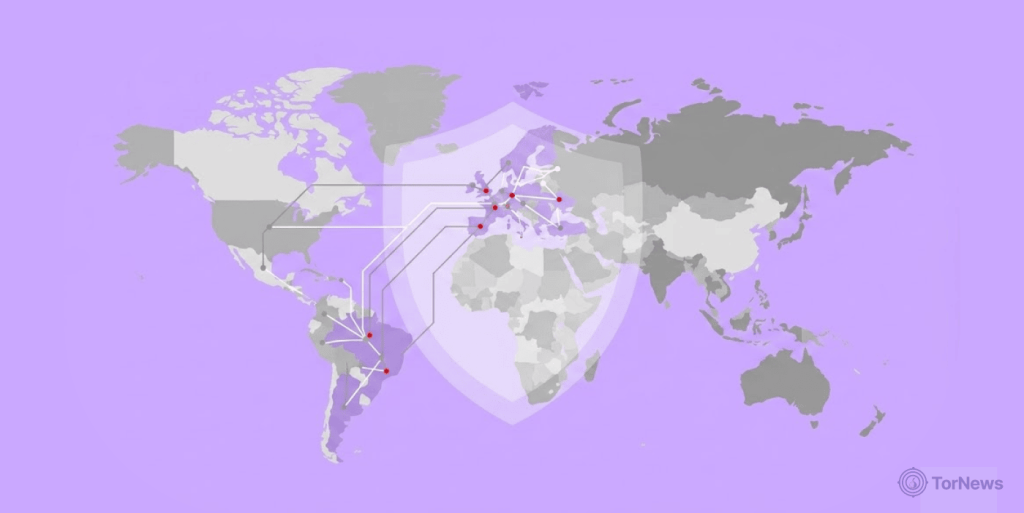
An sophiscated hacker group reportedly linked to China has been quietly targeting South American and southeastern European agencies.
Cisco research team reported the hacking group they refer to as “UAT 8302”. This group of hackers began their activities towards the end of 2024 and reportedly collaborates with other groups linked to China through shared tool kits.
A Shared Playbook Among Chinese-Aligned Hackers
Cisco Talos researchers Asheer Malhotra, Jungsoo An, and Brandon White put out a detailed report about this group. They believe UAT-8302 is an advanced persistent threat, or APT, that’s linked to China.
That’s a fancy way of saying it’s a well-funded, patient group that breaks into networks and stays hidden for a long time. They targeted government entities in South America first. Then later in 2025, they moved to government agencies in southeastern Europe.
The attackers used custom malware that connects them to multiple other Chinese-aligned threat clusters. Talos researchers Jungsoo An, Asheer Malhotra, and Brandon White published a report today. They said the malware connects UAT-8302 to several publicly disclosed threat clusters. This suggests a close operating relationship between them.
The group’s toolkit is impressive and alarming. One key weapon is a backdoor referred to as NetDraft or NosyDoor. It is a C# version of FINALDRAFT (or Squidoor) built on .NET, a common software framework. NosyDoor has connections to at least five other known hacker groups, including Ink Dragon, Earth Alux, and REF7707.
Different security firms have different names for the same group. A Russian cybersecurity company called Solar also spotted NosyDoor being used against Russian IT organizations.
They tracked a group called Erudite Mogwai (A.K.A Space Pirates or Webworm) using it. Solar calls the malware LuckyStrike Agent. Meanwhile, cybersecurity firm ESET tracks NosyDoor use under a group it calls LongNosedGoblin. Multiple groups, same weapon. That’s the pattern here.
The Toolbox and the Service Model
There are many other tools that UAT-8302 uses. First up is CloudSorcerer. This backdoor has been used in attacks against Russian organizations since May 2024. Then we have SNOWLIGHT. It is a VShell stager threat actors UNC6586, UNC5174, and UAT-6382 use.
The group also deploys Deed RAT (also called Snappybee). This is a successor of ShadowPad. They use Zingdoor too. Both malware families showed up in attacks by Earth Estries in late 2024. Rounding out the list is Draculoader. This generic shellcode loader delivers Crowdoor and HemiGate.
How do they get in? Talos does not know the initial access method yet. Researchers suspect the usual approach. That means weaponizing zero-day and N-day exploits in web applications.
Once inside, the attackers act fast. They conduct extensive reconnaissance to map out the network. They run open-source tools like Gogo for automated scanning. Also, move laterally across the environment. The final stage deploys NetDraft, CloudSorcerer (version 3.0), and VShell.
UAT-8302 also uses a Rust-based version of SNOWLIGHT called SNOWRUST. This tool downloads the VShell payload from a remote server. They set up backup access, too. They use proxy and VPN tools like SoftEther VPN and Stowaway.
A Bigger Pattern of Chinese Hacker Collaboration
This isn’t just one rogue group acting alone. Researchers say UAT-8302’s tool sharing shows a close working relationship with other Chinese-linked groups. And that’s part of a growing trend.
Trend Micro revealed a fascinating model last October. They call it “Premier Pass-as-a-Service.” One group called Earth Estries gets initial access to a network. Then they pass that access to Earth Naga for follow-on exploitation. They’ve been partnering with each other since at least late 2023.
This model clouds attribution efforts. It makes it harder to tell which group did what. Trend Micro explained that this service cuts down the time needed for reconnaissance and initial hacking. By skipping straight to the good stuff, the second group saves time and reduces risk. Researchers believe access through this service stays limited to a small, trusted circle of threat actors.
International collaboration isn’t limited to hackers. Law enforcement agencies worldwide are also sharing intelligence and resources to combat dark web crime. In a recent example, Thai police worked with global partners to arrest three Swedish nationals in a major darknet drug trafficking investigation. Learn more, Thai police arrest three Swedes in global darknet drug trafficking probe.
The Talos researchers summed it up clearly. They said UAT-8302’s malware connects it to several previously known hacking groups. All of those groups have been assessed as China-linked or Chinese-speaking by multiple independent industry reports.
Government agencies in South America and southeastern Europe now know they are in the crosshairs. For everyone else, this is a reminder that state-sponsored hackers don’t always work alone, and their coordination is getting sharper.