In today’s hyper-connected digital landscape, individuals and businesses rely heavily on online platforms for operations, transactions, and data storage. While this shift brings convenience and efficiency, it also opens the door to growing cyber threats. Cybercriminals are increasingly targeting sensitive data, leading to financial losses, reputational damage, and a decline in customer trust.
As these risks continue to evolve today, organizations can no longer afford to take cybersecurity lightly. This is where cyber threat management becomes essential. By proactively identifying, analyzing, and mitigating potential threats, businesses can safeguard their systems and maintain secure operations.
In this guide, we’ll break down everything you need to know about cyber threat management, including how it works, the tools involved, and why it plays a critical role in modern cybersecurity strategies.
What is Cyber Threat Management?

Cyber threat management involves activities that identify potential dangers to data, detect them in time, and determine what actions to take after damage has occurred.
Organizations must steadily check information to know where they store it, how they use it at endpoints, and especially how it moves outside the safety of the organization’s network. When on transit outside the company’s network, information is very open to attacks.
Cyber threat management deals with a thorough look at the organisations network and checking for where possible attacks can come from, weak spots and close them up quickly.
Due to the fact that it has become difficult for internet fraudsters to bypass a company’s network, criminals usually seek weak spots in the system to exploit. In some cases, people accidentally leak information, giving fraudsters an easy opportunity.
It needs constant monitoring of the organisation’s network and the grouping of information according to their sensitivity or importance. When organizations sort data into categories, they determine the level of security based on its importance.
Also, not everyone in the organisation should have access to some information. Organizations should grant access to data only to workers whose job responsibilities require that information.
Security systems also note and flag unusual staff activities related to information so that security personnel can investigate them further. Due to how demanding it is to manage threats to data, some organisations give out the management of their network’s security to a third party, usually a cyber security platform.
How Cyber Threat Management Works
For cybersecurity to work, organizations must continuously monitor information on their networks, analyze and group data based on importance, spot unusual activities and raise alerts, encrypt data both at rest and in transit, and train staff to handle threat management effectively.
- Asset and risk identification: The security unit or system checks the entire network of the organisation, seeking for weak security spots and stopping possible threats before they become a problem and patching up such weak points.
- Threat intelligence: Threat intelligence involves collecting and analyzing data on how threats operate, their patterns, and entry points. This insight helps organizations understand attack motives and stop threats before they cause damage. It is a core part of threat management systems, enabling effective detection and prioritization of risks.
- Asset inventory and discovery: Effective threat detection requires full visibility across the entire network. This allows security teams to identify and categorize assets, such as endpoints, servers, IoT devices, applications, and cloud services, based on risk and exposure. With a clear view of data flow, usage, and user activity, teams can spot anomalies, detect potential threats early, and respond quickly to suspicious behavior.
- Weak point assessment and scanning: Organizations continuously monitor their networks by scanning applications, software, and systems to identify and fix vulnerabilities before attackers exploit them. Even a single weak point can lead to ransomware attacks, data breaches, financial loss, reputational damage, and legal issues. By combining automated and manual checks, organizations can detect misconfigurations and security gaps early. Regular monitoring is essential to prevent attacks and reduce risks, including those caused by human error.
- Threat prioritisation: Vulnerabilities allow attackers to access systems and disrupt operations, but not all carry the same risk. By assessing exploitability and business impact, organizations can prioritize threats, addressing high-risk vulnerabilities immediately while scheduling lower-risk issues for later remediation.
- Security training and awareness for staff: Most data breaches stem from unintentional human error, making employee training critical. Without proper awareness, organizations remain vulnerable to data loss and cyberattacks. Training acts as the first line of defense—helping staff recognize risks, avoid mistakes, detect threats early, and respond effectively. Equipping employees with these skills prevents many security issues before organizations rely on advanced tools.
- Incident response: Threat management involves a series of actions to handle network vulnerabilities, including identifying, containing, and eliminating threats, followed by preventive measures. While these steps may not be permanent solutions, they help minimize damage and buy time for stronger security implementation. Post-attack responses, such as isolating systems, restoring data from backups, and stopping further breaches, are crucial for quickly resuming operations and reducing downtime.
- Continuous observation: Manual monitoring alone isn’t enough for modern networks. Automated tools like EDR, IDS, and SIEM help detect and eliminate both known and unknown threats, ensuring smoother and more secure operations. However, no single solution is foolproof, combining these tools with regular manual checks is essential for stronger protection.
Why is Cyber Threat Management Important?

There are lots of critical roles that this plays on individual or organisation level like protection of identity, information, log in details, credit card information and many other important or sensitive information. Some of the critical roles of threat management include the following:
Protection Against Advanced Attacks
In today’s world, guarding against attacks have become more advanced because of how innovative these internet fraudsters have become, adapting to new security measures and learning how to bypass them.
To fully protect your information, you need more than one layer of protection like including a two-factor authentication to whatever security check you may have installed.
Others can include the use of VPN to not just hide the ip address from cyber attacks but also to give a false impression of your location.
Safeguarding Important Information
Using threat management helps organisations to keep sensitive data inside their network, making sure that only authorised staff can access it. Also, only staff whose job scope covers such information should have access to it.
This reduces the chances of a staff becoming an insider that leaks sensitive information to either hackers or other serious competitors. People usually lose information through data leaks and human error. This is why training the staff on data leak prevention and the dangers of cyber attacks is very important.
Cloud Security
Since organizations usually store information before transferring it to where it is needed, they need storage facilities. Limited hardware storage capacity has increased the demand for cloud storage.
In fact, most users prefer cloud storage because of its convenience and bigger storage capacity. Unfortunately, since it’s not inside the network of the organisation, it becomes hard to protect and monitor closely.
Hackers usually tamper with this weak point, but advanced threat management systems patch such vulnerabilities. Organizations must properly configure cloud facilities because attackers easily breach misconfigured ones.
To Protect the Finance and Reputation of Organisations
A lot of companies have lost huge sums of money to criminals on the internet who use ransomware for sensitive information. When the wrong people obtain this information, they demand payment from the owner or threaten to leak the information to the public.
Having a good threat management system helps the company to avoid such unnecessary loss of funds. There is also the concern for damage to the brands image as both customers and potential clients will lose whatever trust they had on the company. Businesses may cancel featured deals.
In very bad cases, clients whose information gets compromised may sue the company for damages. To maintain the protection of a brand’s image, strong security tools such as Zero Trust Security, MFA and granular access controls.
Protection of Remote Work
Even after organizations protect their networks, attackers can still compromise endpoints. By endpoint, we mean the users end. As an organisation grows, they expand to other locations.
Organizations must protect devices connected to the network, and they should install security measures on mobile phones, laptops, and proxy servers. These devices can use a VPN or antivirus to close off weak security spots.
Hackers know that the expansion of an organisation presents vulnerabilities which is why they usually target big companies like Apple, Microsoft and others like them.
Grouping of Vulnerabilities
Just as information is grouped according to their sensitivity, so are vulnerabilities also grouped according to the level of exposure and threat it poses on the entire organisation’s network.
The moment these are done, the level of security attached to each weak spot is dependent on the level of possible threat. Analysing weak points in a network helps to patch up these “holes” and keep a better integrity of the organisation’s network.
Better still, it helps the security team decide which weak points to address first and how urgently they need action.
Compliance Practice
To further help to improve on threat management, the organisation is expected to stick to the standards from regulatory bodies. Of course there are severe consequences when companies fail to comply with these standards.
Some of these standards cover industries such as defense, finance and healthcare. Some of these regulatory bodies include ISO 27001, GDPR, PCI-DSS and HIPAA.
What are the Types of Threat Management?
- Next-Generation Firewall (NGFW): This is a network device that keeps tabs with traffic in an organisation’s network, allowing flow of information when it’s safe and blocking possible threats when it’s flagged, especially new threats that are unknown to most organisations. A comprehensive NGFW combines automated and changeable security systems, context awareness, endpoint and network connections.
- Advanced Malware Protection (AMP): Mostly used on users’ devices, these are software applications that stop all manners of viruses, keeping them away from compromising the system.
- Unified Threat Management (UTM): It involves combining different security tools and forming a good system that can be properly controlled in the organisation’s network or a cloud environment. A UTM system is different depending on the needs of the vendor which might include intrusion prevention systems (IPS), a VPN, threat intelligence, application visibility and control, and malware prevention.
- Managed Detection and Response (MDR): Well-trained security experts handle another security service by constantly monitoring the company’s network security systems to spot and respond to attacks. They use automated security tools along with human investigation, which makes the system stronger and less likely to be breached.
- Security Information and Event Management (SIEM): It requires the use of security alerts, event information, logs and threat intelligence. Organizations use customized policies to make threat alerts the most important feature of the security system. Field experts better understand information flow and respond quickly to such threats.
- Extended Detection and Response (XDR): Monitors every aspect of the organisation’s network which leads to good visibility of the network at large by using automated systems together with human investigations when concerns are raised. They seek out threats and put them down as quickly as they are spotted.
- Securitv Orchestration, Automation. and Response (SOAR): The process relies heavily on automation methods that do all the hunting for threats, analysing information and grouping them (including weak points), controlling all the security tools and a fast response to threats. Given that it reduces manual methods, it has become a more efficient way to protect the network of a company by linking up the security teams, working together as one.
An often-overlooked component of threat management is social media monitoring, which helps security teams detect brand impersonation, credential theft, and social engineering campaigns originating on platforms like Facebook, X (Twitter), LinkedIn, and Instagram.
Sources of Cyber Threats
To be able to manage the risks in an organisation’s network, it is critical to know where these attacks come from:
- Phishing: Hackers use deceit in this process by gaining the victim’s trust and convincing the user to click a malicious link that compromises their system, often by encrypting all files on the device and demanding a ransom before decryption. They usually carry out these attacks through emails.
- Advanced Persistent Threats (APTs): These attacks can remain undetected in a system for a long time, secretly compromising more files and information formation.
- Malware: Hackers create them in various forms, such as spyware, viruses, and ransomware, where they demand a ransom.
- Insider: Information breach or loss are usually as a result of the actions of an insider in the organisation which could be intentional or unintentional. In most cases, it is human error. Human mistakes cause most data loss.
Beyond insider threats and technical vulnerabilities, another major risk in the online world comes from platform operators themselves, understanding what an exit scam is helps users and businesses recognize when a service or marketplace may be preparing to shut down suddenly and disappear with user funds or data, a tactic commonly seen on dark web marketplaces and cryptocurrency exchanges.
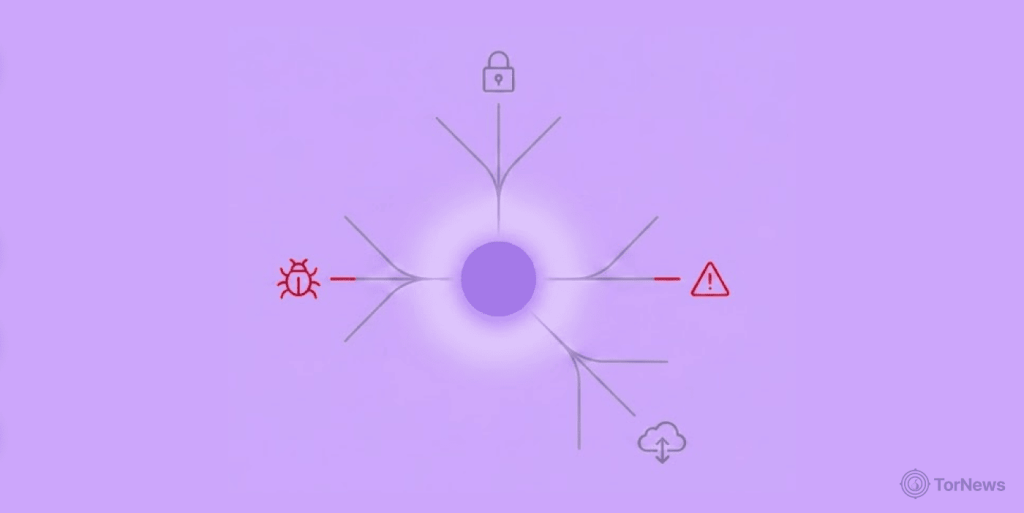
What’s the Difference Between a Threat, Risk and Vulnerability?
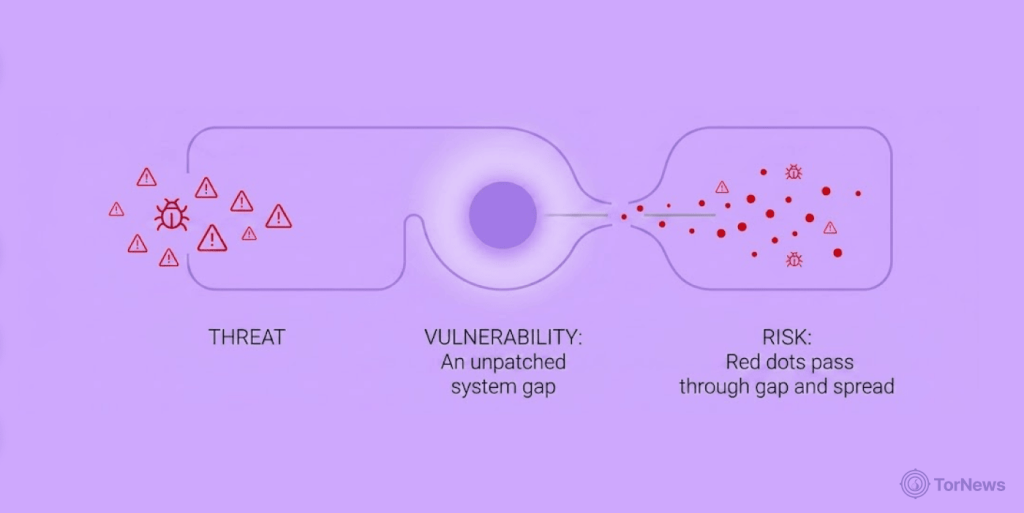
1. Risk
We are discussing the likelihood that a hacker will exploit an attack or a weak point. It is the current situation in the system that determines the risk factor in a system. The aim is to reduce risk factors to a manageable level. It is impossible to completely remove at risks in a system.
2. Threat
Hackers take actions to exploit weak points and gain entry, which makes this situation similar to risk but with a key difference. Whether they succeed or not makes no difference.
Security experts consider actions intended to attack a system as a threat. Intentional threat. A staff member who uses sensitive information of the organisation through an open public WiFi is exposing the information to possible breach. Security experts also consider this a threat.
3. Vulnerability
These are weak spots in a company’s network which can grant access to internet fraudsters if they get their hands on it. Through these openings, information leaks and theft are possible posing a great threat to the network. Organizations should patch such openings before an attack happens.
Difference Between Threat Management and Weak Point Management
Sometimes, the two can be used to replace the other but they are really not the same thing. The table below will educate us:
| Weak point management | Threat management | |
|---|---|---|
| Definition | This is when the security system of an organisation spots weak points, analyses the threat level and groups them accordingly and is able to deal with them before internet fraudsters see them. | A security system checks for possible attacks by spotting them, checking the severity of the attack and stopping them from happening but in real time. |
| Response time | In weak point management, the security unit usually takes their time to crosscheck the whole network for weak points. The threats are not immediate. Weak points are spotted through thorough monitoring and then patched up. | This deals with identifying a possible attack while it’s about to happen and acting quickly in real time to stop the attack from doing damage. It is usually very urgent and should be noticed when damage is done. |
| Main focus | Find out where weak points exist in the network and systematically patch them up, leaving no room for outsiders to exploit. | Identify and quickly deal with cyber attacks as they are happening in real time. |
| Objective | To reduce the chances of possible attacks by dealing with areas where the attack could come from. | To understand how dangerous cyber attacks are and getting rid of them. |
| Process | This includes a complete and thorough assessment of the network and identifying areas where attacks can come from or where possible leakage can happen. | The process includes constant monitoring(real-time), threat intelligence, threat identification, response after an attack and threat management. |
| Example | Unpatched openings are seen and quickly patched up to reduce chances of a possible attack. | Attacks such as phishing through emails are blocked to reduce data loss and damage to brand image. |
Best Practices for Effective Cyber Threat Management

Managing threats and vulnerabilities gives an organisation a more secured network to work in, reducing the potentials for attack and reducing weak points in the network. Some of the best ways to do this include:
- Organizations document and store the threats and weaknesses they experience for future prevention improvements and audits.
- Spotting all the assets the organisation has in the network which include endpoints, servers, IoT devices and cloud environments.
- Grouping these assets according to their importance and patching up existing weak points for the ones that matter the most.
- There should be a response drill to train the security team on what to do when an attack happens, doing it within the shortest possible time.
- The organizations discover misconfigurations, weak points, and software vulnerabilities and patch them before internet fraudsters find them.
- Find out the purpose of each attack and where they come from by using AI tools.
- Access to sensitive information should be given only to workers in the department that covers such information. Granting access to few persons goes a long way to reduce data breach caused by an insider, knowingly or not.
- A threat and vulnerability policy should be provided to detect how the security framework should operate. It needs to be a strong policy too.
- Log in passwords should be strong to reduce chances of credential theft.
Common Challenges in Cyber Threat Management
Despite the advantages of threat management systems, teams still encounter challenges while carrying out these tasks. Let’s take a look at some of them:
- No validation: Unfortunately for most security measures, there is no way to confirm if they really work until there is a breach or data loss. At this point, the situation has already caused damage.. That’s why organizations must test the effectiveness of their threat management systems to ensure they work and must do so continuously.
- Alert fatigue and resource limitations: A threat management system can generate too many alerts, making it hard for security teams to respond effectively. Frequent false alarms can also cause alert fatigue, which makes teams overlook real threats. To address this, organizations must prioritize and analyze alerts based on risk levels, focusing on high-priority issues while minimizing unnecessary notifications from low-risk sources.
- Prioritisation issues: Not all network risks carry the same weight, yet many organizations struggle to prioritize them, leading to false alerts and fatigue. A comprehensive threat management system provides full visibility, helping teams focus on high-risk vulnerabilities while ignoring low-priority noise. As cyber threats constantly evolve, it’s crucial to regularly update and improve security measures rather than relying on outdated systems.
- Poor networking: Poorly connected network components make it difficult to monitor systems effectively, increasing the risk of missed vulnerabilities. However, organizations that integrate their networks well improve visibility across all assets, enable early threat detection, and prevent anything from being overlooked.
- Poor information update: When a security system takes too long to analyze a network, it delays updates and prevents real-time visibility of current threats. This can leave vulnerabilities unnoticed and increase the risk of missing active attacks, putting the organization at greater security risk.
The Next Level: Validation of Threat Exposure

Closing Up the Gap in Conventional Cyber Threat Management
The cyber threat management systems normally try to detect attacks and neutralise them which is good. However, most security checks have not really confirmed the system’s effectiveness. The organisation simply hopes it works and makes assumptions they work because there hasn’t been an attack so far. There has to be a way to verify if the system is functional.
Luckily, there is a way to perform some tests. Ever heard of Threat Exposure Validation (TEV) ? Instead of depending on a monitoring system that is not active, using TEV will definitely put an organisation’s network to test using real-world situations. By doing this, the organisation will be sure that when real threats come, the security check will handle it with ease.
How Threat Exposure Validation Works
- Connects defensive methods with real life attack situations.
- Helps organisations to identify weak points in their network which criminals can exploit in real life situations.
- Also, it shows how a company responds when they eventually see vulnerabilities, like a drill test. Prepares the organisation to respond quickly and effectively.
- Teams conduct the process continuously to evaluate how effective the security system is at all times, rather than treating it as a one-off activity that could leave blind spots.
- The process focuses on the system’s actual configuration rather than assumed weaknesses.
Benefits of Using TEV Tools
Threat Exposure Validation Impact provides several benefits, which are briefly discussed below. According to industry reports and vendor studies, brands that used it enjoyed the following benefits.
- About 37% of organisations said they enjoyed constant confirmation and adjustment of security controls.
- 47% of organisations reported they experienced improvement in security controls relating to detection and prevention.
- 44% of companies who used automated security systems acknowledged a better experience in threat management, especially in the area of managing and patching weak points.
- 41% of organizations expressed high confidence in the security checks’ ability to handle whatever threats arise.
- 47% noticed a shorter response to threats.
- 40% of companies were able to defend against new threats to their networks.
As we can see, TEV improves organizational productivity by keeping operations running with minimal interruptions and reducing downtime when it occurs.
Who Benefits Most from Security Exposure Validation?
The following types of organisations are the one who benefited the most from Security Exposure Validation:
- Companies going through changes: Organisations that are going through infrastructural or digital changes. Such transitions often create multiple vulnerabilities that teams need to patch.
- Information sensitive companies: Organisations that have a lot to lose because of the nature of their operations and how sensitive they are.
- Regulated industries: Platforms that stick to standards like NIS2 and other alternatives.
- MSSPs: Providers check to confirm and show the effectiveness of service.
Key Benefits of Security Exposure Validation
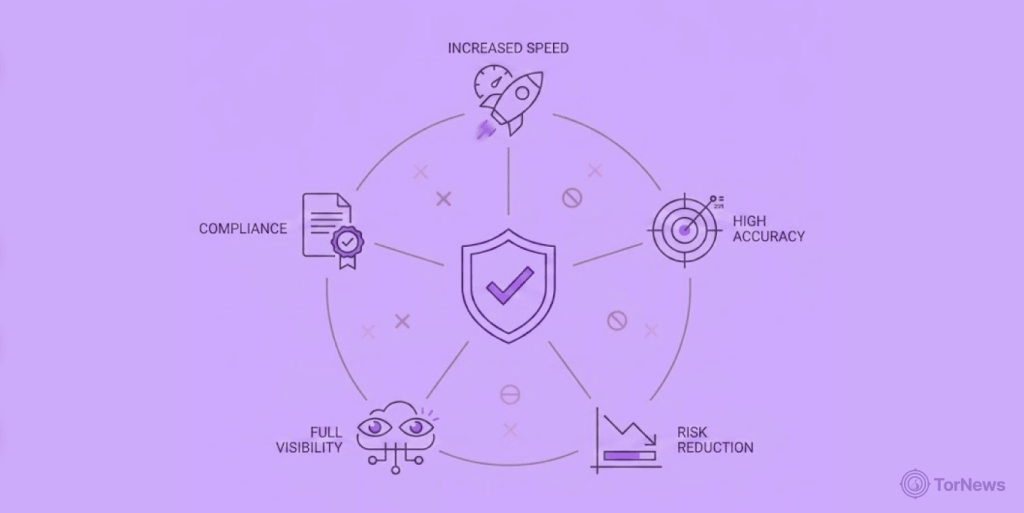
- Closing the gap in skill set: Because these tools are typically automated, they operate continuously with high efficiency without fatigue, unlike human workers, and eliminate the need to hire experts to manage vulnerability assessments.
- Risk grouping: With these tools, it is no longer necessary to patch up every single weak point in the company’s network. Instead, teams prioritize high-risk threats, which reduces false alarms, strengthens protection where it matters most, and saves both time and effort. It’s a win-win situation.
- Active response to immediate threat: With the help of AI tools can imitate attack situations in the real world to test the solidity of the security system to observe weak points in the network. It uses the exact same procedure, paths, and techniques of real cyber attacks to put the threat management to test and push it to its limits.
- Reporting and compliance: Because of how good they are at keeping networks safe, they are always ready to show security documents that are available for auditing and they use programs like ISO 27001, DORA and NIS2.
- Steady security check: It keeps track of the organisation’s network for 24 hours. Teams perform it continuously rather than occasionally.
Closing Word
Cyber threat and vulnerability management is essential for keeping operations smooth, protecting data, and maintaining customer trust. It helps prevent costly breaches, safeguards a company’s reputation, and reduces legal risks.
While automated tools strengthen security, combining them with other solutions and proper staff training is crucial, as human error remains a major cause of data loss.
To build a comprehensive defense strategy, start by understanding the most dangerous threat facing organizations today, read our complete guide on what is a ransomware attack to learn about infection vectors, the double extortion model, and proven prevention techniques.