-
Cofense researchers discovered a phishing scam where attackers use LiveChat to impersonate Amazon and PayPal agents and steal credit card and MFA codes.
-
The scam doesn’t rely on fake websites alone, cybercriminals chat with victims in real-time, making the theft feel like legitimate customer service.
-
Once attackers collect login credentials and phone verification codes, they bypass security measures and drain victims’ accounts.
A sophisticated phishing campaign is fooling people with something they trust: live customer service chat boxes.
Cofense researchers just exposed a clever new scam. Cybercriminals are now using LiveChat software to pose as support agents from Amazon and PayPal in real-time conversations.
The Cofense Phishing Defense Center uncovered this operation. Attackers use a software-as-a-service tool called LiveChat to engage victims directly.
This makes their scam feel incredibly authentic. You’re not just looking at a fake webpage anymore. You’re actually talking to someone who seems like they work for these companies.
Emails that Hook You in
Attackers start the operation with carefully crafted emails. These messages stand out because they use psychological tricks that actually work. One variant mimics a PayPal notification. It tells you that a $200.00 USD refund awaits you. The email includes a button labeled to view transaction details.
Another version keeps things vague. It simply states that an order is pending and requires your confirmation. Both emails contain links using the domain lc.chat. These links don’t take you to a static phishing page. Instead, they open a live messaging box powered by LiveChat software.
This is where things get interesting. You land in what looks like a standard customer service chat. A helpful agent or bot appears ready to assist you. Cofense researchers found that cybercriminals customize these chat boxes to perfectly mimic brands like Amazon and PayPal.
Live Conversations Real Theft
The Amazon version features a fake agent who engages in back-and-forth conversation. Researchers noticed the agent’s language often appeared messy and unprofessional.
Strange greetings like “Ello” and odd punctuation like “Hello !” or “Open chat !!” appeared frequently. This suggested a real person was typing responses rather than running an automated script.
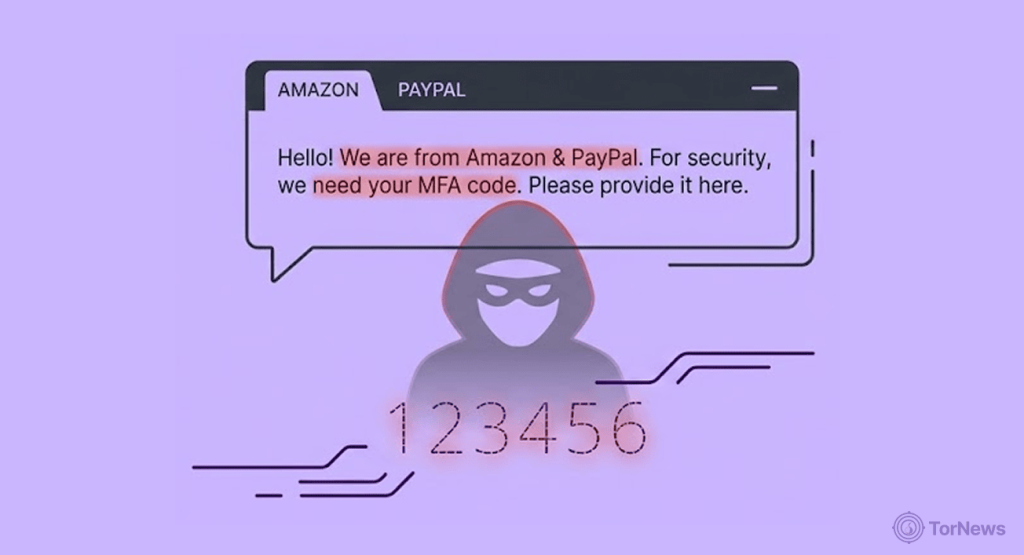
During these conversations, threat actors ask for everything. They request personally identifiable information, including names, addresses, phone numbers, and dates of birth. They push for banking details such as complete credit card numbers, expiration dates, and CVC codes. But they don’t stop there.
Attackers also try to capture multi-factor authentication codes. These are the one-time security passwords that services send to your phone to verify your identity. Getting these codes is the golden ticket for cybercriminals.
The scammers often reassure victims throughout the chat. They promise that your data will be “handled with the utmost confidentiality.” This false sense of security keeps people sharing information. By the time the chat ends with a polite thank you, attackers have already collected everything they need.
Why this Method Works So Well
Live chat makes the entire scam feel legitimate. We’ve grown accustomed to resolving issues through these boxes on real shopping sites. Our natural defenses drop when we see a familiar chat interface. That’s exactly what attackers count on.
Once scammers collect a victim’s login credentials and phone verification code, they can completely bypass security systems. The Cofense report explains that attackers can then “drain the user’s financials” by seizing full control of the account. The damage happens quickly and often goes unnoticed until it’s too late.
The sheer volume of credentials stolen through these methods becomes evident when breaches like the alleged PayPal leak surface, over 100,000 sets of login details appearing on the dark web in a single dump, each representing a victim who likely encountered a scam not unlike the live chat scheme described here.
Cofense researchers emphasized the evolving nature of these threats. “We highlighted two threats that combine brand impersonation, social engineering, credential theft, identity theft, and other techniques that demonstrate the rapid evolution and integration of threats,” their report states. “These cases highlight why human-driven analysis remains essential.”
The best defense remains healthy skepticism. Unexpected refund offers should always raise red flags. Legitimate companies rarely initiate contact about refunds through unsolicited emails. If you receive such messages, visit the company’s official website directly rather than clicking any links.
Contact their verified customer service to confirm whether the communication is real. That extra step could save you from a costly mistake.