-
A database from the Russian cybercrime forum RAM leaked, exposing 7,707 users, 1,732 threads, and more than 340,000 IP records.
-
This forum was a marketplace where access sellers, ransomware gangs, and brokers from 20+ countries gathered, more like a one-stop shop for cybercrime.
-
Based on the leaked data, it was deduced that U.S. government agencies, banks, and hospitals took the hardest hit from the activities going on this marketplace.
A leaked database from the Russian cybercrime forum RAMP showed us what a high-level ransomware market actually looks like inside.
Security researchers looked into the data, which inclides 1,700 threads, 7,700 users, and thousands of IP logs. What they found? This platform runs like a real business, organized and very detailed set up, almost like how big legit industries operate.
What the Leak Reveals About a Hidden Economy
Security site Comparitech got exclusive access to the full MySQL database dump, and it exposes every activity that went on on RAMP spanning a period of 27 months. They found user records, forum posts, direct messages, IP logs, even admin activity.
Surprisingly, the database held thousands of user accounts (like about 7,707). And also, it contained hundreds of forum discussion threads. The IP logs alone exceeded 340,333 entries.
People traded nearly 1900 private chats, which boiled down to about 3,900 messages. In addition, you’d find fourteen ransomware-as-a-service programs that bad actors advertised on the site. Plus links to over 250 leak sites.
All these show that RAMP wasn’t some small hideout. It was a large, mature criminal marketplace with lots of activity going on daily.
The forum was eventually targeted by law enforcement, the FBI shut down RAMP in a significant seizure operation, and the database analyzed by researchers came from that takedown, providing an unprecedented look into the inner workings of a major ransomware-as-a-service platform.
How the Ransomware Chain Worked on RAMP
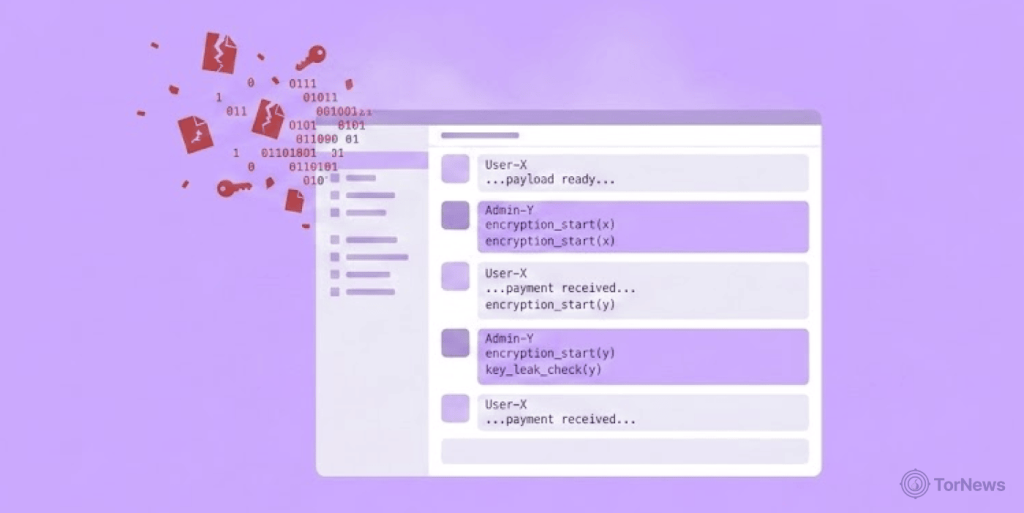
The forum supported every step of a ransomware attack. It was a full-service shop. Criminals could buy network access, find partners, trade tools, and recruit affiliates.
The access market was especially busy. The database shows 333 separate threads selling entry into compromised corporate networks. Getting inside a network is usually the hardest part when launching an attack. Once in, the rest of the work is much easier for the attackers.
The ransomware-as-a-service section had 60 threads. Some offered affiliates up to 90% of ransom payments. With a split like that, ransomware keeps pulling in new people. It’s a criminal business model built to grow.
Who Got Targeted and What Was for Sale
The leak also reveals the victims. Some examples of RAMP’s targets are banks, hospitals, defense contractors, energy companies, technology firms, and government agencies. They went after over 20 countries, with the US appearing on 40% of listings containing country identifier information.
The attacks targeted Government agencies more. Roughly twenty posts targeted them directly. Finance and banking tied with tech and telecom at 11 listings each.
Attackers weren’t chasing easy marks. The chased victims who can’t afford to say no. Downtime hurts. Data leaks causes even more damage. The organizations pay up because the alternative is a heavy financial loss.
The private messages added a hidden layer to all this. The total conversations in the database were 1,899, private messages nearly 3,900. Criminals used these to discuss VPN access, stealer logs, and partnership requests. Public posts advertised goods. But private chats closed the deals. One access broker alone posted 41 separate listings, acting like a wholesale supplier.
Why This Matters for Defenders Today
RAMP shows why ransomware won’t fade away. The forum helped criminals specialize. One person steals access. Another sells malware, while another person launches the final attack. This type of delegation is what made ransomware quicker, less expensive, and much more difficult to disrupt.
Law enforcement has been trying, but their efforts don’t solve the issue because when you shut one forum down, another one springs up quickly. One forum down, and the ecosystem just fragments and moves. Criminal markets adapt instead of disappearing.
So what should organizations do? Focus on practical controls. Reduce exposed services and external access paths. Enforce MFA everywhere possible. Detect unusual login behavior. Monitor the dark web for your corporate credentials. Improve your incident response before an attack actually happens.
The RAMP leak shows you how ransomware really works. It’s not just about the encryption at the end. It’s a whole market that makes the attack possible from step one.