-
Starbucks discovered unauthorized access to Partner Central accounts on Feb. 6, 2026, affecting 889 U.S. employees.
-
Attackers used fake websites mimicking Partner Central to steal login credentials and access sensitive employee data.
-
The exposed information includes Social Security numbers, dates of birth, and bank account details.
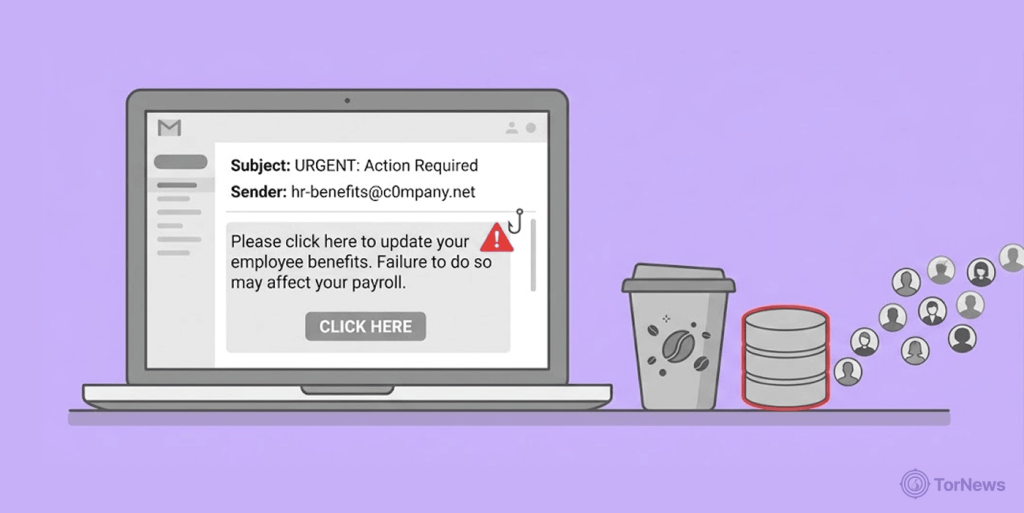
A phishing scheme just caught nearly 900 Starbucks employees off guard. The coffee giant confirmed that hackers tricked workers into handing over their login details through convincing fake websites.
Starbucks said it is working on determining what information the unauthorized entry accessed. According to the company, the unauthorized user did not gain access through a firewall or exploit a software flaw but rather through the use of counterfeit websites that look exactly like the original website.
How the Attack Unfolded
Starbucks knew about the incident on Feb. 6, 2026. The company immediately launched an internal investigation with the help of cybersecurity experts. The investigation revealed that attackers had set up phishing websites designed to impersonate Partner Central’s login page.
Employees who fell for the scheme entered their usernames and passwords on these fake sites. The attackers then used those stolen credentials to access the real Partner Central accounts. This type of attack is particularly effective because it bypasses traditional security measures entirely.
The breach affected 889 individuals across the United States. Five of those victims were located in Maine. Once inside the accounts, the attackers gained access to highly sensitive personal information. This included employees’ full names, Social Security numbers, dates of birth, and even financial account numbers with routing information.
Starbucks officially disclosed the breach to the Maine Attorney General on March 12, 2026. The company sent written notification letters to all affected individuals two days earlier, on March 10, 2026.
Company’s Response and Support Measures
Starbucks gave affected employees 24 months of free access to Experian IdentityWorks. This comprehensive protection package includes several key features. Credit monitoring will alert employees to any changes in their credit reports. Internet surveillance will scan the dark web for their personal information up for sale.
The service also provides identity restoration assistance. Additionally, the package includes $1 million in identity theft insurance coverage.
Employees don’t need to provide a credit card to enroll in these services. They can access identity restoration help immediately, even before formal enrollment is complete. The company has also issued detailed guidance on protective steps employees should take right away.
This guidance includes monitoring financial accounts closely for unauthorized transactions. Starbucks recommends changing passwords immediately, especially for anyone who reused their Partner Central password on other accounts. Employees can also place fraud alerts with credit bureaus or request full security freezes to prevent new account creation under their names.
Steps to Stay Protected
So how do you protect yourself from similar attacks? Phishing schemes like this one are becoming increasingly sophisticated. The fake websites often look nearly identical to legitimate login pages.
Always verify the URL before entering any credentials. Check that the web address matches the official company domain exactly. Look for the secure lock icon in your browser’s address bar. Be skeptical of any unsolicited emails or messages asking you to log in urgently.
Never click links in emails that direct you to login pages. Instead, manually type the website address into your browser or use a saved bookmark. Enable two-factor authentication wherever possible. This adds an extra security layer that makes stolen passwords much less useful to attackers.
Monitor your financial accounts and credit reports regularly. Set up alerts for unusual activity. If you’ve reused passwords across multiple sites, change them immediately. Each account should have a unique, strong password. Consider using a password manager to keep track of them all.
These precautions are essential because once your data is stolen, it can be packaged and sold, as seen in the Chilean credit card trafficking case, where a single defendant sold thousands of stolen cards, each representing a victim whose life was disrupted by fraud. Starbucks employees affected by this breach should remain extra vigilant. Watch for suspicious activity on bank accounts and credit cards.