-
A ransomware group exploited a critical Cisco firewall flaw as a zero-day for 36 days before the company fixed it.
-
Amazon’s security team spotted the attackers through its MadPot honeypot system and tracked down a server loaded with their full set of tools.
-
These criminals use a combination of their own malware and legitimate programs to steal data, retain access to the system, and pressure victims to pay ransom.
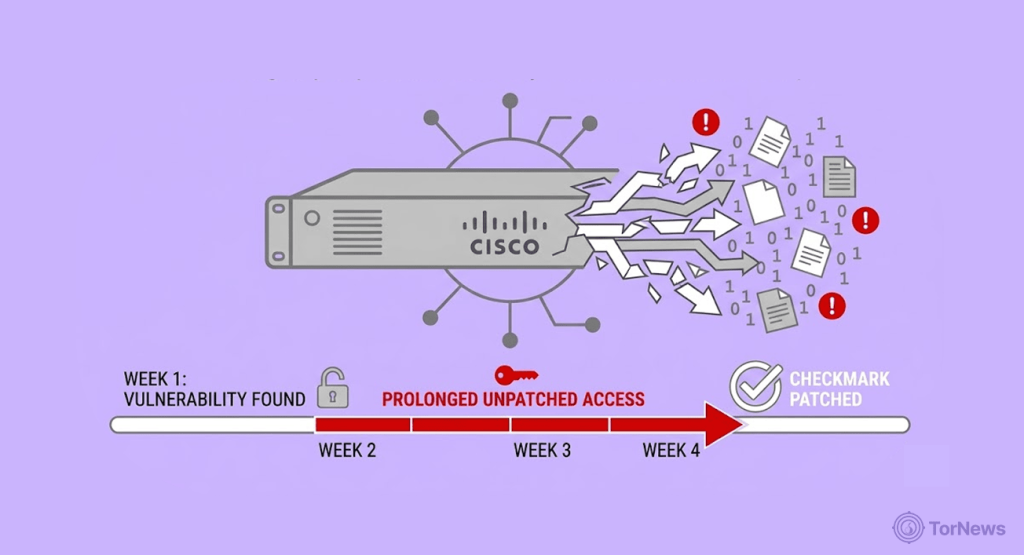
Interlock, a ransomware gang, took advantage of a bug in Cisco’s firewall for more than a month until Cisco finally released a fix.
This flaw lets remote attackers execute any Java code as root without authentication on vulnerable devices. Amazon’s honeypot network later detected the attack and exposed the attackers’ full toolkit.
The Cisco Security Flaw that Allowed Hackers in for a Whole Month
Amazon’s top security boss dropped a bombshell this week. Ransomware criminals had already been exploiting a maximum-severity Cisco bug for over a month before the company even knew about it.
CJ Moses, the chief information security officer at Amazon Integrated Security, shared the finding on Wednesday. His team discovered that the ransomware crew Interlock started abusing the flaw on January 26. Cisco didn’t release a patch until March 4. That’s over a month of the attackers coming and going as they pleased with no one raising an alarm.
The flaw is a weakness in Cisco Secure Firewall Management Center software tagged as CVE-2026-20131. It’s a critical security hole. With this hole unpatched, anyone can run malicious Java code remotely as root on affected devices. No authentication needed. This means complete takeover of the device without any questions.
A spokesperson for Cisco thanked Amazon for alerting them and also confirmed they’ve updated their security accordingly. They urge every user to implement the fix by updating their systems immediately.
Interlock’s History of Attacks
Interlock isn’t your run-of-the-mill cyber gang. This crew emerged last year and quickly made a name for itself by hitting the most vulnerable targets.
The group infected the kidney dialysis firm Davita and Kettering Health. At Kettering, they didn’t just encrypt files. They messed up the chemotherapy sessions and pre-surgery appointments. And to make matters worse, they leaked the personal information of cancer patients online.
Over the summer, Interlock claimed responsibility for stealing 43 GB of files from Saint Paul, Minnesota. This led to the city declaring a state of emergency due to the number of people it affected.
How Amazon Caught The Attackers
Amazon didn’t go looking for Interlock specifically. The criminals walked right into a trap.
The company operates something called the MadPot honeypot network. More like a field of fake, vulnerable targets designed to lure attackers in. When Interlock took the bait, Amazon logged all the exploit traffic tied to their infrastructure.
Then the security team got lucky. They spotted a misconfigured server on Interlock’s side. That server accidentally exposed the group’s entire attack toolkit. It was like finding the thieves’ blueprint lying on the street.
This toolkit has been used in numerous high-profile breaches, including the University of Phoenix attack that exposed 3.5 million records on the dark web, proving that once a gang’s methods are understood, the full scope of their victim list becomes painfully clear.
Inside Interlock’s Digital Toolbox
The exposed toolkit reveals just how thorough these criminals are. It starts with a powerful PowerShell script that vacuums up everything from victims’ Windows computers.
The script grabs operating system details, running services, installed software, and storage configurations. It catalogs Hyper-V virtual machines and lists user files from the Desktop, Documents, and Downloads folders. It even scoops up RDP authentication events from Windows logs.
Browser data isn’t safe either. The script grabs all it can, bookmarks, saved passwords, and even extensions from browsers, be it Chrome, Firefox, Edge, Internet Explorer, and 360. It then packages and compresses everything into ZIP files, naming them after the host for easy theft.
Further, Moses explained the scale of this attack. He noted that this per-host output is proof that the script runs across multiple machines in a network. That suggests the attackers are gearing up for organization-wide encryption.
The Backup Plans Within Backup Plans
Interlock doesn’t put all its eggs in one basket. The group uses multiple custom remote access trojans, or RATs, to maintain control.
One JavaScript implant cleverly overrides browser console methods to hide from detection tools. It then collects system identity, domain membership, username, OS version, and privilege context. It encrypts this data and ships it to command-and-control servers through persistent WebSocket connections.
The implant also provides interactive shell access and can execute any command. It moves files in and out, sets up SOCKS5 proxies to tunnel traffic, and even updates itself. If needed, it can delete itself on command.
If that wasn’t enough, the attackers dropped a second implant written in Java using GlassFish libraries. It does the exact same things. Two identical implants in different languages means if defenders catch one, the criminals still have a backup.
Amazon also found a Bash script that turns Linux servers into HTTP reverse proxies. It wipes logs every five minutes and survives reboots. Additional Java files include a memory-resident backdoor that never touches the disk, making it invisible to traditional antivirus tools.
Blending In With Legitimate Tools
Here’s where it gets really clever. Interlock also uses perfectly legitimate software alongside its custom malware.
They often deploy ConnectWise ScreenConnect, which helps them take control of remote desktops. Then make use of Volatility, which is an open source tool, for memory forensics. Also, the attackers use Certify to find and exploit misconfigurations in Active Directory Certificate Services.
Moses went on to explain that when cybercrooks mix legitimate tools with their own custom malware, they’re buying insurance. If you remove one backdoor, they’ll still have another way to get in.
Amazon tied all this activity to Interlock using an ELF binary, an embedded ransom note, and a TOR negotiation portal. The ransom note adds a nasty twist. It threatens to report victims to regulators, using the pressure of fines and compliance violations alongside data encryption and leaks to force payment.
This is to tell how thorough these crooks can be. They do their homework before embarking on any campaign: study the target, build redundancies into their attacks, and then use every pressure point they can find.
For security teams, Amazon’s findings provide a detailed look at exactly how these criminals operate, which is a rare find. Now it’s up to organizations to patch that Cisco hole before Interlock or someone like them, comes knocking.