In 2026, activism no longer unfolds only on the streets, it lives in encrypted messages, private networks, and decentralized platforms.
As governments expand digital surveillance and AI-powered monitoring becomes the norm, secure communication is no longer optional for activists; it is essential for survival.
From protecting identities to safeguarding entire movements, the way activists communicate today directly shapes their ability to organize tomorrow.
This guide breaks down the most effective secure communication best practices activists must adopt today to stay private, resilient, and one step ahead of increasing digital scrutiny.
Understanding Threat Models
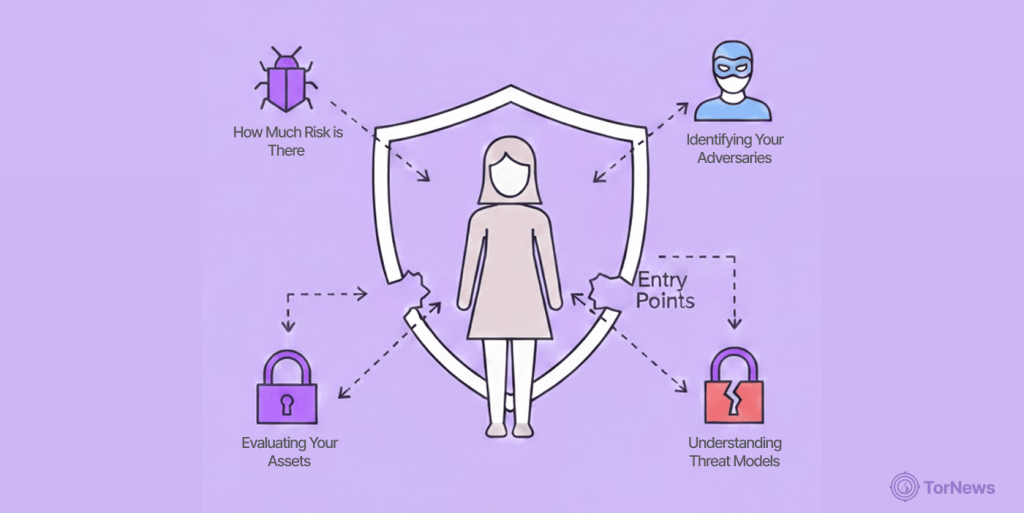
In 2026, you cannot protect everything from everyone. Defining your threat model is the first step toward effective activist digital security.
Identifying Your Adversaries
Determining who your opponent is will let you decide on the best security measures for them, whether they are local, state, or federal agencies or companies that sell your personal information.
Evaluating Your Assets
Understanding precisely what to protect will help you identify how to protect them—your membership list, meeting locations (private and public), or financial records. These days, who you talk to and when you do so is often worth more to bad guys than what you actually said.
How Much Risk is There
Risk is a function of both threat and vulnerability. As a result of this, different privacy tools for activists for different levels of privacy concern will be applied when organizing your local community garden, as opposed to your involvement with whistleblowing with other similar high-risk operations. Always prioritize protecting administrative access to your group’s digital infrastructure.
Encrypted Messaging Platforms

Standard SMS is a data goldmine for surveillance. In 2026, you must use platforms that leave no digital trail on central servers.
The Gold Standard: Signal
Signal remains a top recommendation because it collects virtually no metadata. For activists in 2026, ensuring that “disappearing messages” are enabled for all sensitive chats is a mandatory protocol.
Decentralized Alternatives: Session and Briar
If you’re looking for the ultimate anonymity, Session is your better choice as there is no requirement for users to sign up with their mobile number. In cases of total internet shutdowns, Briar can provide secure local communications via Bluetooth or Wi-Fi and can bypass state-controlled internet service providers.
Caution Against Common “Secure” Apps
Don’t trust WhatsApp or Telegram for anything that matters. These apps may be encrypted, but they collect lots of information about you (metadata) or don’t provide end-to-end encryption (E2EE) for all group chat messages, only some.
Don’t put your movement at risk with apps that have weak privacy models. Stick to the vetted recommendations in our guide to the best secure and encrypted messaging apps to ensure your communications are truly private.
Metadata-Free Communication Protocols
The metadata associated with your communications could expose your true identity regardless of whether or not they have been encrypted. Tools such as Tor Browser and VPN (such as NordVPN) provide methods to hide your IP address and therefore prevent your exact location from being revealed.
Operational Security Fundamentals

Operational security, or OPSEC, is the behavioral side of privacy. Even the best tools fail if your habits are poor.
Device Hygiene and Encryption
In 2026, your phone must be encrypted. Use a 6+ digit alphanumeric passcode instead of biometrics (FaceID/Fingerprint), as many legal systems can compel you to provide a fingerprint but not a password.
Password Management and 2FA
Use a trusted Password Manager such as Bitwarden and enable MFA on all accounts, but discard using SMS Text Codes. Use hard token codes, such as YubiKeys, instead.
Keeping Tabs on Your Digital Footprints
Conduct regular reviews of your online identity. Delete old accounts and use “masked” emails or temporary numbers for activist registrations to prevent your digital life from being linked to your real identity.
Compartmentalization Strategies
Keep your activist life and personal life separate. Never use the same devices or email addresses for both. Use hardened operating systems like GrapheneOS to isolate sensitive data.
Meeting Security

Physical meetings are high-risk zones in 2026 due to advanced biometric tracking and facial recognition.
Secure Physical Locations
Select places for meetings away from public access points for Wi-Fi and avoid areas where dense amounts of CCTV are installed and monitored.
This caution is more important than ever. The recent dark web spy ring busted in South Korea, over 120,000 hacked IP cameras, is a chilling reminder that surveillance networks can be turned against citizens by criminals and state actors alike. Assume any camera in a public space could be compromised.
Hardware Protocols for Meetings
The “no-phone” rule is essential. Phones are tracking beacons. If you must bring one, use a Faraday bag to block all signals, or leave devices in a secure location blocks away from your meeting.
Verification and Trust Building
In 2026, “Deepfake” technology will make digital verification harder. Always verify new members through in-person verification or pre-established “safety numbers” on Signal before sharing sensitive details.
Digital Organizing Tools

Managing a movement requires more than just chat; it requires secure, private coordination.
Secure Document Collaboration
Avoid Google Drive for sensitive planning. Use E2EE alternatives like CryptPad or Proton Drive to ensure that even the service provider cannot read your organizational documents.
Private Calendar Management
Regimes often use intercepted calendars for “preventative arrests.” Use encrypted calendars like those offered by Tuta to keep your movement’s timeline private.
Internal Polling and Voting
During a voting process for an organization, when members want to vote in a manner that preserves their right to remain anonymous, utilize different platforms including Loomio and encrypted forms that do not allow tracking of IP addresses.
Social Media Security

The ability to use social media as a means of getting together is certainly an asset, but it can also have negative consequences regarding the information one exposes about themselves.
Minimizing Public Exposure
Never mark yourself as “Going” to a protest on public platforms. Use social media only for broad announcements and move coordination to secure, encrypted platforms.
Managing Anonymous Profiles
If you maintain an activist persona, use a secure connection and a “clean” browser. Ensure your posts do not contain unintentional metadata, such as identifiable background landmarks in photos.
Combating Misinformation and Bots
In 2026, AI bots are used to derail movements with “noise.” Establish trusted channels for your community and train members to verify information before resharing.
Legal Considerations

Digital security must be paired with an understanding of your local legal landscape and rights.
Knowing Your Rights in 2026
Laws regarding digital privacy change rapidly. Understand the “Right to Encryption” in your jurisdiction. In some regions, “Lockdown Mode” on your device provides a crucial legal barrier.
Managing Data Retention Laws
Many countries have implemented mandatory data retention for ISPs. This makes a reputable no-logs VPN mandatory to prevent your browsing history from being stored for government review.
Prepare for Digital Subpoenas
Assume that any data held by a third party (Google, Meta) can be subpoenaed. The goal of secure communication for activists is to ensure that when a subpoena arrives, the provider has no data to give.
Protecting Vulnerable Members

The ability to use social media as a means of getting together is certainly an asset, but it can also have negative consequences regarding the information one exposes about themselves.
The security of any organization is dependent upon the vulnerabilities of each of its members; therefore, your organizational approach is to have every member act as a role model for one another in regard to the safe use of digital tools.
Specialized Support for High-Risk Individuals
Activists in high-conflict zones face higher surveillance. Provide these members with extra resources, such as hardware security keys and dedicated secure “burner” devices.
Building a Community of Care
As you grow and develop, you are required to band together to provide care for other activists; therefore, we must form a “buddy system” to provide one another with emotional support, digital hygiene monitoring, and if someone feels that their device has been compromised, let the “buddy” know.
Why Anonymity is a Collective Responsibility
If one individual in a network uses an unencrypted SMS to communicate regarding a meeting, this creates a point of failure for the entire (secure) network.
As it relates to communication for activists in 2026, it will be extremely important to establish a culture of secure communications and to train all members of the organization to promote secure communications to ensure no one accidentally compromises the network or those within the network.
Responding to Compromise
Even with the best OPSEC, breaches happen. Your response defines your movement’s resilience:
Incident Response Protocols
If a member’s device is seized, have a “kill switch” protocol. This includes remotely wiping shared documents and removing the compromised member from all encrypted group chats immediately.
Recovery and Learning
Performing an analysis of a breach to identify the contributing factors is an important first step in recovery. It should also be used as a training opportunity to improve the security posture of the group as a whole while avoiding shaming the individual involved in the breach.
Long-Term Sustainability

Burnout can contribute to an increased security risk in the long run. If you are tired, you make mistakes that compromise the group.
Security as a Habit
Don’t wait for a crisis. Make these secure communication best practices for activists in 2026 part of your daily routine, so they become “muscle memory.”
Mentorship and Training
The overall security knowledge should not be held by a small group of security professionals. Consistently offer learning activities to teach new staff members the fundamentals of cryptography/encryption and metadata management.
Balancing Security and Accessibility
Security should not make your movement impossible to join. Create “on-ramps” where new members can learn basic security before being given access to high-stakes information.
International Considerations
In 2026, the internet is becoming even more fragmented with national firewalls and national restrictions.
Navigating Cross-Border Surveillance
If your activity is international, data crosses borders with different privacy regulations. Use end-to-end encrypted technologies that are “jurisdictionally agnostic,” where the end-to-end encryption will survive any legal jurisdictional challenge.
Tools for High-Censorship Regimes
In highly censorial nations, conventional VPNs may be illegal or unavailable. Use “obfuscation” technologies, such as the Tor Network, to access government censorship challenges where there is no an alternative connection.
Common Mistakes to Avoid in The Field

- Trusting “free” VPNs: Most of these will record your data and sell it to third parties.
- Using public Wi-Fi: Never sign into high-profile accounts while connected to a public Wi-Fi system, unless you have several protections in place.
- Oversharing on social media: Hackers can easily impersonate members of your private group.
- Ignoring software updates: A lot of today’s security problems take advantage of old weaknesses that the software vendors have already fixed.
- Using personal or corporate email for organizing: Standard email providers like Gmail or Outlook are not encrypted and are prime targets for subpoenas. Always use one of the best secure email services for any activist-related correspondence.
Best Practices Summary
To stay safe in the shadows, follow these core pillars of 2026 activist digital security:
The Activist’s Daily Checklist
- Verify “disappearing messages” are active on all chats.
- Update your device software immediately to patch vulnerabilities.
- Disable biometrics when attending any public event.
- Audit your app permissions and location settings daily.
Parting Word
In 2026, the future of activist resistance depends on secure, private communication and protection from AI-driven surveillance. Adopting secure communication practices isn’t just about configuring tools; it’s about building a resilient culture of resistance.
This requires shifting from convenience-based apps to hardened, decentralized platforms and developing disciplined digital habits that minimize metadata exposure. Privacy is not a crime; it is the foundation of a free society.
Activists must remain skeptical of corporate “security” claims and practice strong digital hygiene, including the use of physical security keys and air-gapped devices for sensitive work.
Ultimately, the goal is to reduce exposure. Reclaiming digital sovereignty today ensures that the movements you help build can survive escalating surveillance tomorrow.
FAQs
Signal is safe for (most) people; however, for activists, Session is more suitable, as it does not require a telephone number nor does it have any type of central server, thus making it extremely difficult to be tracked.
The activist threat model outlines a process for identifying the adversaries who are monitoring the people, along with what they are after (the activists’ assets) and where they may be vulnerable, which then allows the activists to create a security strategy tailored to them.
It is, as long as it is a reputable “No-Logs” provider, such as NordVPN. Although it is extremely important to use VPNs to change your IP Address in order to protect against ISPs and other online entities, it is more effective when combined with the Tor browser for added anonymity.
Before heading to the protest, make sure to activate “Lockdown Mode” (on iOS) or an equivalent software on Android. By activating Lockdown Mode, you disable any biometric unlocking methods (FaceID/Fingerprints) and only use a unique, strong alphanumeric passcode. This will make it much more difficult for law enforcement to obtain access to your phone in many jurisdictions.
If you are involved in higher-risk situations, then it would be safer to purchase a prepaid phone that is not connected to your name (either by phone number/IMEI) or home Wi-Fi. A phone that does not have any association with your name will allow for a greater degree of separation and anonymity once an action has occurred.