-
A dark web user named Donny Brasco claims to possess secret US defense documents and wants payment in Monero (XMR).
-
The offer follows a separate February 2026 claim of 49 Pentagon documents being sold on Telegram.
-
The DOD previously suffered a real breach in 2023 that exposed over 20,000 employees’ personal data via an unsecured cloud email server.

A threat actor named Donny Brasco is selling alleged US Department of Defense documents on a dark web forum.
Experts haven’t verified the claim yet, but the offer alone raises serious national security concerns.
A Troubling Dark Web Listing
The threat actor using the name Donny Brasco posted that he has American Department of Defense documents for sale on a forum called Tenebris. The post asks interested buyers to message him on Session, an encrypted chat app.
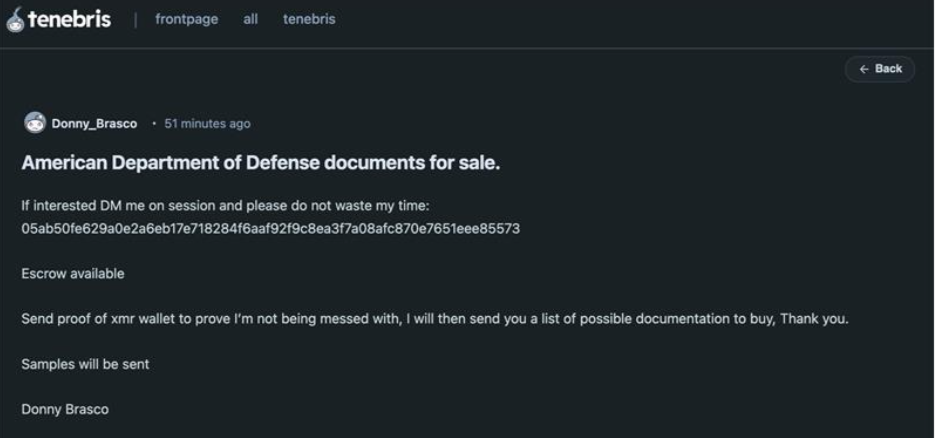
He wants proof of a Monero wallet first. It’s worth nothing that Monero is the preferred payment currency on many cybercriminal forums right now because it makes transactions hard to trace.
The actor promises that he’ll send a list of available documents after he receives the proof. He also says escrow is available, which is a way to hold funds safely during a deal.
Here’s the catch. No recent reports confirm the DOD suffered a data breach. Security experts haven’t looked into the claim yet. So this could be a bluff. But even a fake offer deserves attention. Why? Because selling fake classified docs still threatens national security. It wastes law enforcement resources. And it creates panic.
Previous DOD Data Breach
This isn’t the first time the Department of Defense has appeared in a data breach. In early 2023, the agency detected a breach which affected the private information of 20,000 employees. Surprising, the victims only got to hear about it February 2024. The DOD never provided an explanation for their delay.
The root cause? A DOD service provider left emails “inadvertently exposed to the internet.” The affected email accounts contained personally identifiable information, which may have included names, addresses, Social Security numbers, and other sensitive personal information.
The DOD sent a letter to affected people. In the letter, the agency said there’s is no evidence suggesting a misuse of the victims’ PII. It also urged people to sign up for identity theft protection.
Based on report, the breach came from an unsecured Microsoft cloud email server. The server was likely misconfigured. Anyone on the internet could access it without a password.
Government data exposure isn’t limited to the US. In a separate but equally alarming incident, fake government portal leaks passports and personal documents of 1,100 Bangladeshis to dark web, showing how fraudulent government websites can become a goldmine for identity thieves when sensitive citizen data ends up on criminal marketplaces.”
In a statement, the DOD said they’ve fixed the problem and also revealed that they fished out the affected server removed it from public access. They added that the vendor resolved the issues.
Another Actor Claims Pentagon Documents for Sale
This isn’t the first time someone offered sensitive defense files this year. In late February 2026, a different threat actor claimed to have 49 sensitive Pentagon documents. Security researchers flagged the listing as critical. Federal authorities are still checking if the documents are real. But the underground cybercriminal community is already talking about it.
The seller claims this is a “hand-picked” collection. Not a mass data dump. According to reports, the archive contained very sensitive info – internal memos, briefing documents, technical schematics, even communication logs. The seller said they only use Telegram for inquiries. That tactic helps avoid law enforcement tracking.
We don’t know how Donny Brasco got his documents. Maybe he hacked the DOD directly. Maybe he bought an old data dump. Or maybe he has nothing at all. The truth remains unclear for now.
Implications of the Leak in National Security
Here’s the real dangers – even a small batch of documents can help adversarial nations. Defense logistics, military readiness, or internal policy shifts help enemies map US strategies. They can also find weak spots in critical infrastructure.
There are two likely sources for this kind of leak. One is an insider threat, like Jack Teixeira in 2023. The other is a supply chain breach, like the Leidos Holdings leak in 2024.
If a defense contractor suffered a hack attack, it’ll affect many agencies. When hackers get their hands on metadata from real documents, they can launch targeted spear phishing attacks. A DOD employee might open a malicious attachment if it references a real internal memo.
Doctored documents also fuel disinformation campaigns. Adversaries can leak fake files through pro-Russian Telegram channels. That sows discord among US allies. It also erodes public trust in defense institutions.
Possible Response and Mitigation Strategies
So what should the DOD do right now? First, defense contractors and agencies need an emergency audit. Look for unauthorized export or print actions involving groups of around 50 files. Second, enforce hardware-based multi-factor authentication. Physical security keys stop account takeovers.
In addition, audit every third- party vendor access. Limit permissions to the least privilege needed. Record and monitor every remote session. Finally, brief employees to treat unsolicited documents with extreme caution. Use official channels to verify the authenticity of files and never click on links from sources you’re not sure of.
For now, Donny Brasco remains a mystery. But his claim, true or false, forces us to take dark web threats seriously.