-
Scope of the breach, a threat actor named “scatt3r” is selling 28GB of compressed data. This includes 14 databases with around 29 million rows covering visa appointments for countries like Canada, Spain, and China.
-
Extremely sensitive assets, beyond customer data, the hacker also obtained backend source code, SSH private keys, Amazon S3 bucket dumps, and MySQL ROOT access. This means the attacker could potentially control BLS’s internal systems.
-
Biometric data exposed, the leak contains liveness videos from OzForensics, passport scans, national ID cards, and residence permits. This type of data is nearly impossible to change if misused.
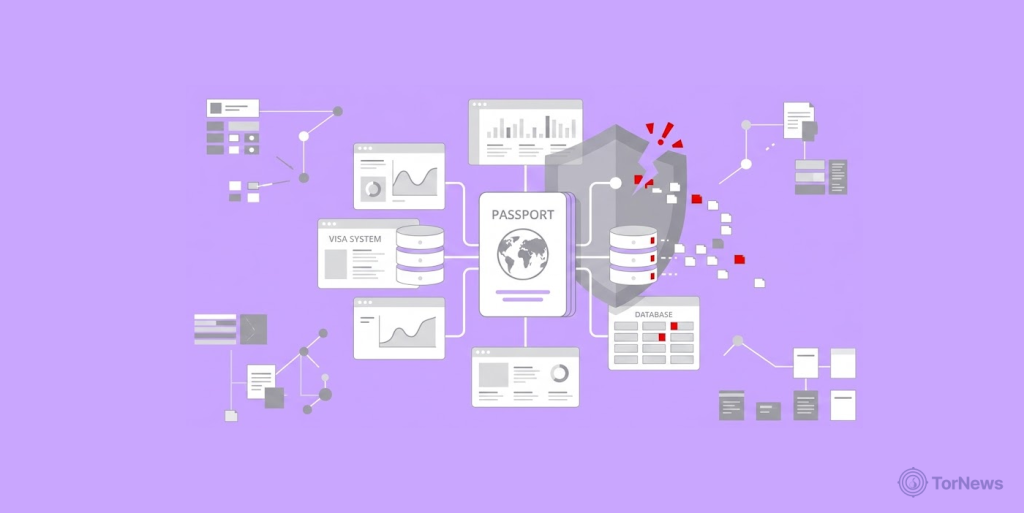
A threat actor who goes by the name Scatt3r claims that they obtained a database containing 29 million records from BLS International, which is an Indian visa processing company.
The information that he has reportedly obtained consists of biometric pictures of individuals and scans of their passports, as well as having full root access to BLS’s servers.
A Breach of Global Visa Infrastructure
Someone just posted a very detailed sales ad on DarkForums. The seller goes by “scatt3r.” They claim to have broken into BLS International. That is the Indian company that processes visas and passports for dozens of governments worldwide.
According to this hacker, he is selling the entirety of the things that he allegedly obtained. The total amount of data is approximately 28GB of compressed files. That includes 14 different SQL databases.
These databases cover visa appointments for India with Kuwait, Canada, UAE, Spain, Singapore, Malaysia, Hong Kong, and China. There are also databases for Poland in the Philippines and a backend for Brazil-Lebanon.
But the hacker did not stop at customer lists. They also stole the backend source code for BLS’s web application. That code includes PHP files, configurations, .htaccess rules, and mailers.
Even worse, the attacker claims to have full MySQL ROOT access. They also have SSH private keys to the backend servers. This means a buyer could log into BLS’s systems as if they were an administrator. They would not need a password or permission.
What Kinds of Data Did the Hacker Take?
The post lists folders full of personal documents. We are talking about PassportApplication folders with actual passport scans. There are national ID cards, residence permits, and biometric face photos.
The hacker also stole liveness videos. These are short recordings made during in-person visa appointments. The service OzForensics apparently powers that feature.
Each applicant has a CUST_ folder ID. That ID ties together their appointment data, documents, and biometrics. The hacker also grabbed private API keys, SMTP keys, and SMS API keys. Internal admin templates and the captcha system are also up for sale.
What This Means if the Breach is Real
This is not a typical data leak. If true, this breach puts the entire national security process at risk. Embassies and consulates rely on BLS to verify who is entering their countries. A hacker controlling that data could issue fake visas or illegal real people.
The biometric data matters most. You cannot reset your face or your fingerprints. Once those videos and ID scans hit the dark web, identity thieves can use them forever. They could open bank accounts or pass border checks in your name.
The targeting of visa data is a growing trend. A hacker recently claimed to have stolen UAE investor data, including Golden Visa records, demonstrating that cybercriminals see immigration and visa processing systems as high-value targets.
Also, SSH keys and root access give a buyer ongoing control. They could watch live data or plant malware inside BLS’s network. Governments using BLS might need to re-evaluate their contracts entirely.
How Potential Victims Can Stay Safe
If you have ever used BLS for a visa, act now. First, freeze your credit with all three bureaus. That stops criminals from opening loans in your name.
Be very careful with your email and phone for phishing scams. Bad actors often use real passport numbers to get unsuspecting people to fall victim to their tricks. Avoid engaging with any links that come with unsolicited text messages or emails, go to the embassy or consulate’s official website instead.
Further, you can try replacing your passport with a new one if you’re scared the current one might be compromised. Many countries offer this service if you report identity theft. In addition, you should also contact the embassy where you applied for your visa, as they could potentially mark your file as having been compromised.
Finally, use different passwords across all websites and use a good password manager. The leaked records likely contain your email and personal information as well, so reusing one password across all sites might increase the risks.
BLS has not yet confirmed the breach publicly. But the dark web post includes very specific file folders and database names. It looks credible. For now, treat your personal documents as if they are already for sale.