-
With its malicious advertisement targeting Spanish-speaking users, the Mirax Android RAT has gained access to more than 220,000 Meta accounts.
-
The malware uses infected devices to create a SOCKS5 proxy that allows it to conceal the true IP address of attack victims.
-
Mirax Android RAT uses a malware-as-a-service model, and users can pay $2,500 for a 3-month subscription, and there’s a monthly option for $1,750.
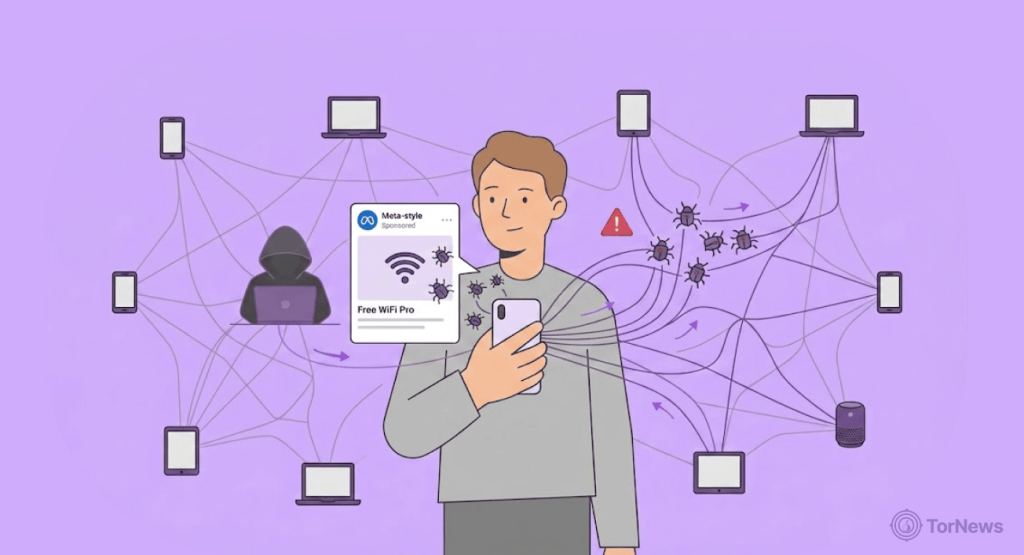
A new Android trojan that turns your phone into a secret backdoor for criminals has emerged. It has already gotten into the devices of over 220,000 people via Facebook and Instagram ads.
How this Malware Infection Spreads
Attackers are running ads on Meta platforms. These ads promise free access to live sports and movies. Six such ads have been spotted so far. Five of them specifically target users in Spain. One particular ad started running on April 6. It alone reached 190,987 accounts.
The ads lead to download pages for a dropper app called StreamTV. This app tricks you into allowing installations from unknown sources. Once you do, it deploys the real malware named Reproductor de video.
What makes this tricky? The criminals use GitHub to host the malicious files. They also add extra protection using tools called Virbox and Golden Crypt. This helps the malware avoid detection by security tools.
What Mirax Does to Your Device When It Gets In
Italian security firm Cleafy broke down the malware’s capabilities. Mirax isn’t just another data thief. It turns your Android device into a residential proxy node.
Here’s what that means. The malware uses SOCKS5 protocol and Yamux multiplexing. These create persistent proxy channels. Attackers can then route their illegal traffic through your real IP address. So when they commit fraud or take over accounts? It looks like you did it.
This same proxy-hijacking capability is found in ‘Albiriox’ Android malware, which is also rented on the dark web and turns infected phones into residential proxy nodes for criminal operations, showing that this functionality is a standard feature in modern mobile malware-as-a-service offerings.
The malware also packs traditional RAT features. It can capture your keystrokes, steal your photos, and even gather lock screen details. It runs commands remotely. In addition, it even watches your screen activity in real time.
Mirax sets up three separate communication channels. One on port 8443 for remote access. Another on port 8444 for stealing data. A third on port 8445 for the proxy function.
A Controlled, Expensive Operation
This isn’t your average malware. Researchers say access is highly controlled. The operators of the Mirax MaaS prefer Russian-speaking actors with a solid reputation in the underground scene.
Details about Mirax first surfaced last month when security researchers spotted a threat actor named ‘Mirax Bot’ offering paid access to a private MaaS on dark web forums.
Users can access the malware for three months at $2,500. But there’s also a lightweight option of $1,750 per month, which doesn’t come with the proxy or Google Play Protect bypassing capability features.
And get this: when the malware lands on your phone, it doesn’t pop up with anything suspicious, it just looks like a regular video player. It asks for accessibility services. Then it shows a fake error saying installation failed. All while running hidden in the background.
Cleafy notes this marks a shift in the threat landscape. Residential proxy abuse used to come from hacked smart TVs or cheap IoT devices. Now it’s inside full-featured banking trojans.
Each infection now has more monetization potential. Attackers can commit direct fraud. Or they can use your phone as infrastructure for wider crimes. The exact final goals aren’t fully known yet. But the targeting of Spanish-speaking countries and the use of streaming lures suggest a well-planned campaign.
Your best defense? Don’t just sideload random apps from unknown sources. And social media ads? Some of them are traps wrapped up as shiny deals. Think twice before clicking.